These 'smart' home devices could be the biggest security threat to your entire company
From teddy bears to Teslas, nothing is safe, experts warn

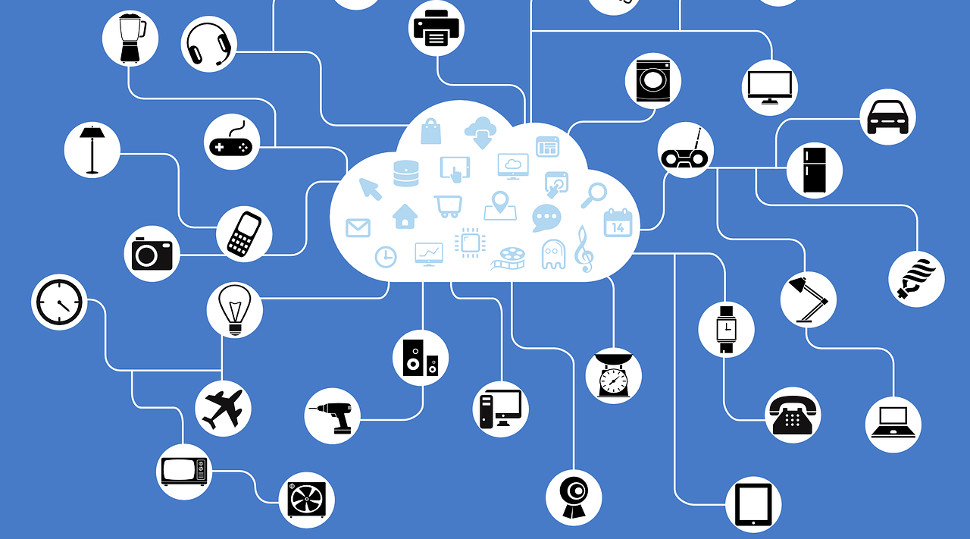
So-called 'smart' devices could be posing a major security risk to not just your home network, but to that of your business too, experts have warned.
The huge rise in Internet of Things (IoT) devices in recent years has greatly widened the threat attack landscape for criminals to target, with devices from smart fridges, thermostats and even toys being released to the public with insufficient security protection.
Now these devices are appearing more frequently in homes and offices around the world, they are beginning to pose serious questions concerning potential security access to corporate networks.
- These are the best ransomware protection tools around today
- And here are the best business VPN services
- Get rid of any issues with the best malware removal tools
IoT threat
A report by Palo Alto Networks surveying business leaders around the world found a rise in the number of IoT devices connecting to business networks over the last year, including connected trash cans, light bulbs and hand sanitizer stations.
Overall, nearly half (41%) of those polled said they need to make a lot of improvements to the way they approach IoT security, and 17% said that a complete overhaul is needed.
Nearly 1 in 4 of those surveyed at larger organizations reported that they have not segmented IoT devices onto separate networks, and only one in five (21%) claimed to follow best practices of using microsegmentation to contain IoT devices in their own tightly controlled security zones.
Palo Alto says that its research shows there’s a need to do more in order to close the gap in IoT security strategy, with billions of IoT devices expected to be activated in the next few years.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
"Visibility really is key to both realising the business opportunity and understanding the risks of IoT," said Greg Day, VP and chief security officer, Palo Alto Networks.
"This is because most devices use proprietary methods, which are increasingly encrypted. If you cannot tell what a thing is or what normal looks like, how can you define what it should be able to access and why? More critically, how do you spot a change, that could be good, new capabilities or bad with the device being used as a gateway for attack."
"With the influx of IoT, including the supply chain sub-dependencies that they add, organisations should not assume they are adequately secured. There is a lack of standardisation in security controls and the value of IoT devices varies so wildly between a few to millions of pounds. So, we can't expect the same investment in security controls when the IoT asset value varies so greatly."
“IT and security teams need to embrace visibility of IoTs and then segment both their critical digital business assets and align IoT things only to the business processes required. In other words, micro-segmentation."
- Best endpoint protection software - keep your endpoints safe from the ever growing number of threats

Mike Moore is Deputy Editor at TechRadar Pro. He has worked as a B2B and B2C tech journalist for nearly a decade, including at one of the UK's leading national newspapers and fellow Future title ITProPortal, and when he's not keeping track of all the latest enterprise and workplace trends, can most likely be found watching, following or taking part in some kind of sport.

 Become a TechRadar Insider
Become a TechRadar Insider







