Cisco unveils fog computing to see through Internet of Things
New vision for cloud is anything but murky
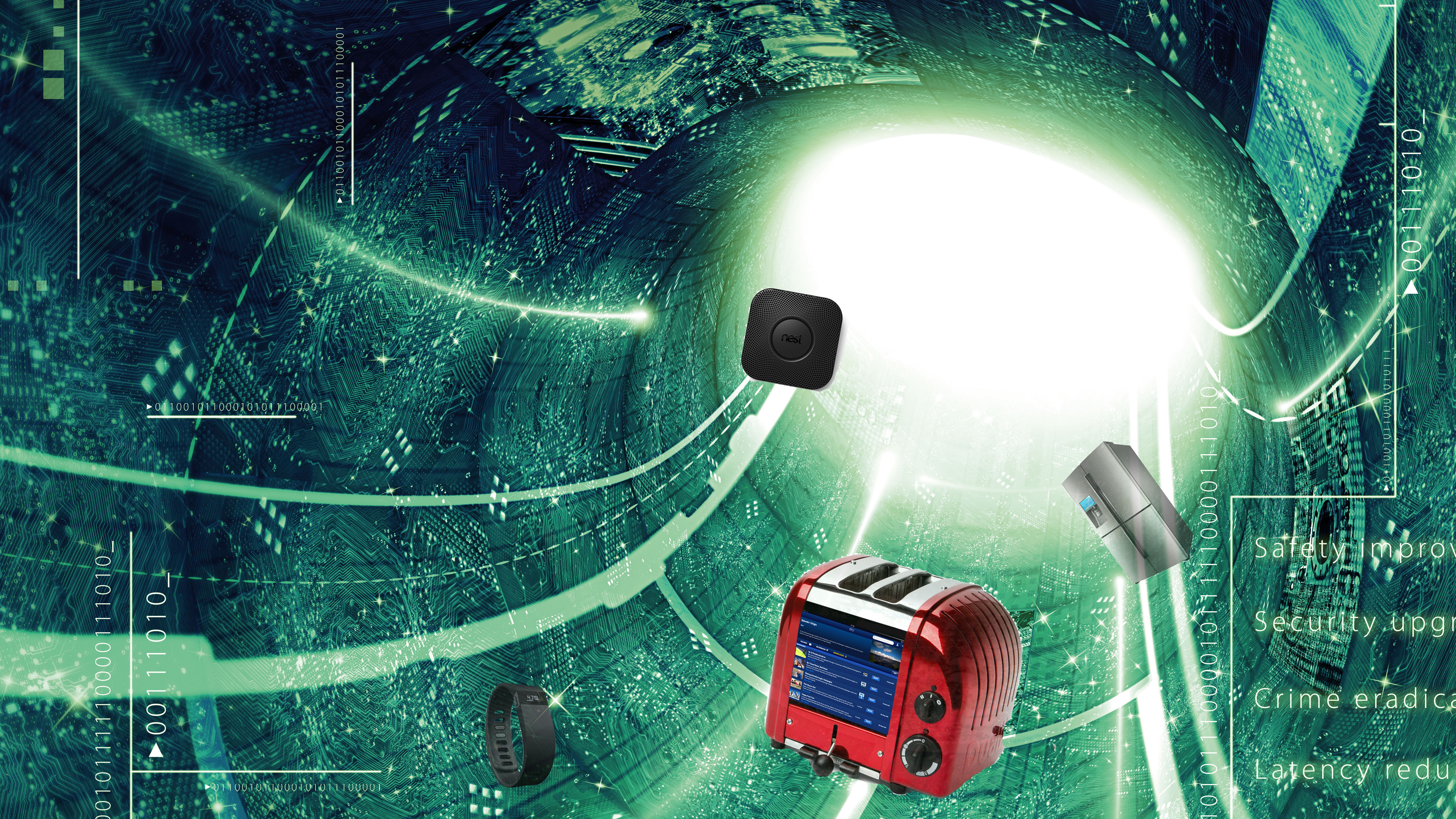
Cisco hopes to connect the Internet of Things to cloud data centres seamlessly by using what it's calling 'fog computing'.
Fog computing, the company says, will be a "highly virtualised platform that provides compute, storage and networking services between devices and cloud computing data centres". This is a solution Cisco hopes will solve main problem of connecting the Internet of Things to internet-connected devices.
Cisco won't, however, be turning routers into massive data-crunching server centres any time soon. The routers will instead be used to carry out simple tasks by processing the signals between the cloud and the "Thing" that is operating within the Internet of Things.
To let its routers to do the computing required to bridge the gap, Cisco plans to combine Linux with its Internetworking Operating System (IOS) to create a distributed infrastructure. The architecture, named IOx, will make it easier for users to connect to industry-specific systems.
Cloudy fog
As well as lowering the amount of data that has to transferred between networks, the fog promises to help devices operate if their connection to the cloud is suddenly lost, storing their data for when the connection is re-established.
"Cisco is very excited to accelerate innovation in the Internet of Things by delivering IOx, which provides the ability to combine computation and communication on our ruggedized routers and other devices," said Guido Jouret, general manager of IoT at Cisco, in a statement. "We believe that this turns the network into the fourth platform for computing, which will unleash new applications in manufacturing, transportation, smart cities and many other industries."
The Internet of Things is already causing a buzz, with reports stating that the tech could be worth trillions to governments around the globe. The IoT can have its downsides, though: devices, even fridges, are all connected to the internet and can therefore be hacked.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!

 Become a TechRadar Insider
Become a TechRadar Insider







