Can businesses stick with Windows XP and still avoid a hacking disaster?
Many organisations are still using XP and old versions of IE
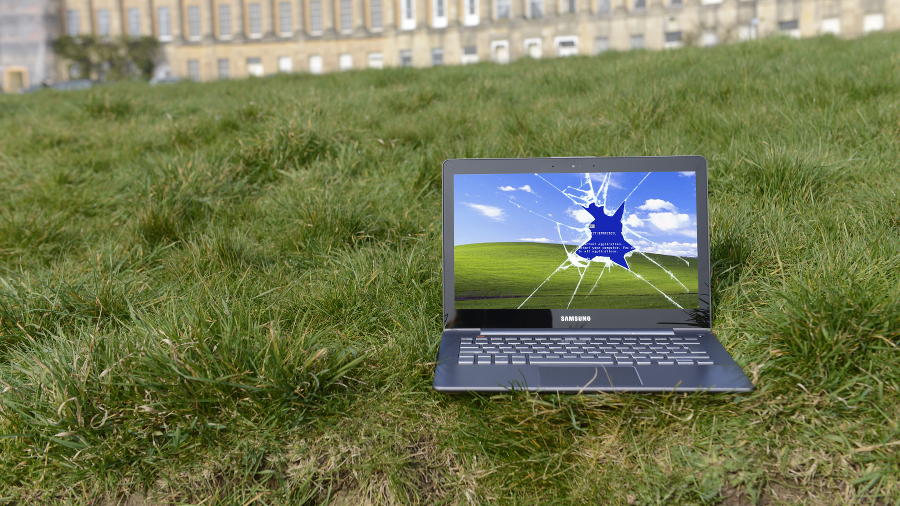
Even though the deadline for any type of support for Windows XP was up last April, many organisations are still using the venerable operating system to power their PCs and the applications that run on them.
But XP was never a truly secure OS to begin with and despite numerous patches over the years, new vulnerabilities have been found. Of course, since April 2014, no more updates have been provided by Microsoft on general release and this has left anyone still running XP very much exposed to hacking and security breaches.
According to figures from IT security firm Secunia taken from scans by its Personal Software Inspector, around 15.17% of computers around the world are still using Windows XP. Nearly 18% of users are still running with an old version of Internet Explorer.
Data protection
Kasper Lindgaard, Secunia's Director of Research and Security, advises that small businesses should definitely migrate away from Windows XP if they want to protect their data.
"Generally speaking, newly discovered vulnerabilities in XP are unpatchable for private users. XP users are 'free-for-all' to hackers, who can create and use exploits at will," he says.
"Additionally, patches to the other Windows operating systems are likely to be reverse engineered by hackers, to discover which vulnerabilities were fixed by Microsoft, and can be modified to work against Windows XP."
Hype and noise
The hype around the XP deadline was similar to that of Y2K, says Sergio Galindo, general manager at GFI Software, and while the date came and went, nothing blew up.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
Galindo notes: "XP attacks do continue, but all the other operating systems remain under attack as well. Although continuing to use Windows XP and older versions of Internet Explorer is unsafe and not recommended, ultimately the question businesses must ask themselves is: how much risk are we willing to take, and how does it compare to the cost of an upgrade?"
Keep on running
But why do firms still insist on running the software? While reasons can range from anything to do with their familiarity with the system, to training requirements or anticipated costs attached to upgrading, the big issue is compatibility as many companies have an aged estate of apps with either OS or IE dependencies, according to HP's Chief Technologist James Morrish.
Microsoft does offer emulation modes, but most companies don't trust this, and the process can be complex to setup and test.
"The challenge is that most businesses have thousands of applications, and typically a Windows 7 migration will also include either extensive application testing or rationalisation and modernisation which would be a huge amount of work," says Morrish. "Many businesses have been avoiding the changeover because they fear the lack of compatibility and loss of productivity during the transition."
"So also, to a certain extent the issue is wrapped up in the cost equation. For the most part, it isn't just that companies can't afford to refresh their hardware, it is that they don't also have the budget and time to test the compatibility of the thousands of applications that the company runs."
Is it possible to safely use XP and IE now there is no more support? It is possible, says Andrew Avanessian, EVP of consultancy and technology services at endpoint security firm Avecto, but he doesn't recommend it.
He says firms that are forced to keep using legacy operating systems can significantly reduce the chance of a cyber-attack by adopting a proactive defence in depth approach to security.
"The default for these old systems is that users are given administrative rights, but removing admin privileges and dealing with the challenge areas with privilege management solutions has been found to mitigate 92% of critical Microsoft vulnerabilities, and can therefore significantly reduce the attack vector," says Avanessian. "Layering other defences on top of that, such as application whitelisting, will mitigate most targeted cyber-attacks."

Rene Millman is a seasoned technology journalist whose work has appeared in The Guardian, the Financial Times, Computer Weekly, and IT Pro. With over two decades of experience as a reporter and editor, he specializes in making complex topics like cybersecurity, VPNs, and enterprise software accessible and engaging.

 Become a TechRadar Insider
Become a TechRadar Insider







