Windows crash reports grant easy access to hackers and spies
Your crash errors might be seen by more than Microsoft
Sign up for breaking news, reviews, opinion, top tech deals, and more.
You are now subscribed
Your newsletter sign-up was successful
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
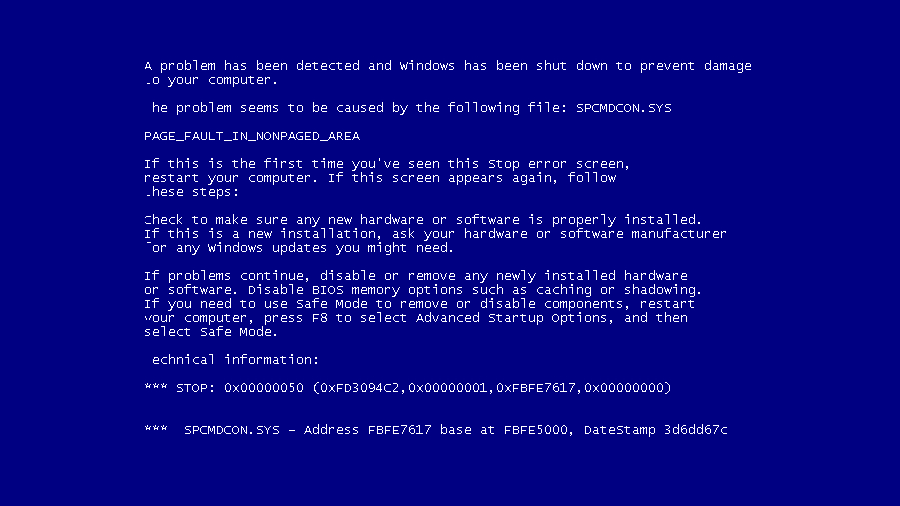
Windows' error-reporting system, which is often used by many at times of frustration with their computer, might be vulnerable to hacking and spying, according to a researcher.
The system sends a wealth of data unencrypted and in the clear, information that hackers or security agencies can use to refine and pinpoint attacks. Documents released over the weekend by Der Spiegel also reveal that the NSA collects Windows crash reports from its wiretaps to target PCs.
The information in a crash report "would definitely give an attacker a significant advantage. It would give them a blueprint of the [targeted] network," said Alex Watson, director of threat research at Websense, which on Sunday published preliminary findings of its Windows error-reporting investigation.
Article continues below"Trivial" for attackers
Microsoft does not encrypt the initial crash reports, said Watson, which include both those that prompt the user before they're sent as well as others that do not. Instead, they're transmitted to Microsoft's servers "in the clear," or over standard HTTP connections.
Windows Error Reporting is installed and activated by default on all PCs running Windows XP, Vista, Windows 7, Windows 8 and Windows 8.1. Watson characterized the chore of turning the cryptic reports into easily-understandable terms as "trivial" for accomplished attackers.
Websense have recommended that businesses and other organizations redirect the report traffic on their network to an internal server, where it can be encrypted before being forwarded to Microsoft. This is complicated, but avoids removing the feature completely. To turn it off entirely would throw away a diagnostic tool that could be useful to IT departments and engineers.
A Microsoft spokesperson asked to comment on the reports said, "Microsoft does not provide any government with direct or unfettered access to our customer's data. We would have significant concerns if the allegations about government actions are true."
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
 Become a TechRadar Insider
Become a TechRadar Insider






