TechRadar Verdict
Nmap is one of the top “old school” open-source network scanners but it isn’t fit for those who don’t have the technical know-how or a thirst for new knowledge at the very least.
Pros
- +
Adaptable to any OS
- +
Free for everyone
- +
It’s splendidly scriptable
- +
Relatively straightforward to use
- +
Scans for various vulnerabilities
Cons
- -
Not the best choice for newcomers
- -
Old-fashioned UI
Why you can trust TechRadar
Network Mapper, or Nmap for short, is a free, open-source network scanner and it’s one of the most recognized tools of this type used by networking experts and white hat hackers across the world. It’s also rather useful in tasks such as network inventory management, scheduling service upgrades, and server or service uptime monitoring.
However, before going any further, let’s hear a bit about Nmap’s background. It was introduced for the first time in September 1997 by security expert Gordon Lyon in Phrack, an online magazine written by and for hackers. Originally written in C, C++, Python, and Lua programming languages, Nmap came a long way from its previous versions.
Although Nmap started its journey as a Linux utility, today it’s available on multiple operating systems (OS’) including Windows, Mac OS, Gentoo, and BSD. Nevertheless, it’s still most popular among Linux enthusiasts.
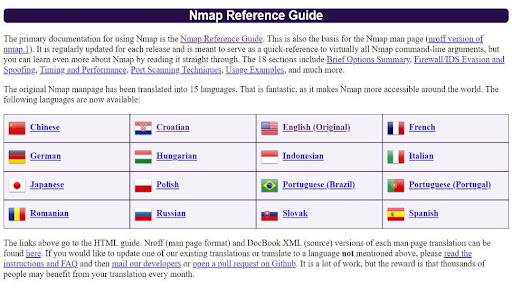
Visiting Nmap’s official site took us back to the not-so-distant past with a web design that withstood the march of time without making any major changes – or any at all. While this makes the site seem old-fashioned and overwhelmingly wordy by today's standards, we found it to be quite charming. Plus, there’s plenty of information about the product itself and in multiple languages to boot.
For news and updates, you can follow Nmap on Facebook, Twitter, Reddit, and GitHub.
Plans and pricing
As mentioned before, Nmap is completely free to download and use, and it’s going to stay that way. As the Nmap community reports, this multi-purpose tool is downloaded a couple of thousand times per week.
According to the brains behind the Nmap, the main mission of this project is to make the internet a bit more secure and to provide administrators/auditors/hackers with an advanced tool to help them examine their networks.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
What’s more, since Nmap is open-source software, anyone with technical know-how can modify and redistribute its code under the license agreement.
Features and functionality
If you have a plan to start a career in hacking (ethical hacking, of course), you’ll surely find Nmap to be more than useful. The same is true if you’re an aspiring cybersecurity expert who wishes to expand your knowledge in network security. So, in either case, Nmap seems to be a smart choice.
It was created with large networks in mind and it can scan them in a trice – however, it works wonderfully against single hosts as well.
Besides the standard command-line Nmap executable, the Nmap suite also comes with an intuitive graphical user interface (GUI), Zenmap results viewer, a command-line tool for reading, writing, redirecting, and encrypting data across a network called Ncat, a tool to aid in the comparisons named Ndiff, and a tool for network packet generation and response analysis going by the name Nping.
Whether you want to utilize Nmap as a network analyzer or packet sniffer, it will prove to be a valuable and versatile tool. For instance, you can run a scan on any internet protocol (IP) that’s active on your network and check if it’s a standard service or an external attack. You’ll also be provided with information about the types of devices, reverse domain name system (DNS) names, media access control (MAC) addresses, and IP addresses of all active hosts.
Interface and ease of use
There’s no need to sign up nor leave any private data to install Nmap – just go to the official site, tap into the “Download” button on the top menu, choose the OS you’re using and check the step-by-step guide you’ll be provided with.
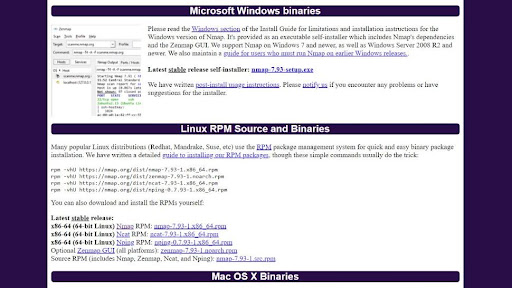
Installing Nmap on Windows is as simple as anything – look for the latest stable release of Windows self-installer and click on the link to download the EXE file. Once it’s done, simply double-click the file and run the installation following the instructions as they show up.
Besides being super simple, the self-installer also provides the option to install the Zenmap GUI and other tools – so, don’t skip text. After the installation is complete, go to the “Executing Nmap on Windows” section and find out how to execute Nmap on the command line or through Zenmap.
If you’re using Linux you can opt between a source code installation and several binary packages – although there is a pretty detailed how-to, it can be a bit tricky for less experienced users.
On Mac, you’ll get a dedicated installer, and if you’re using Kali Linux or Parrot OS, Nmap comes pre-installed.
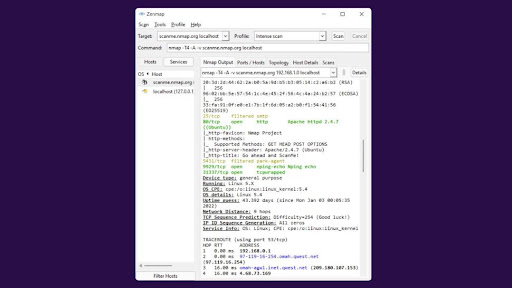
While Nmap’s UI (that’s Zenmap) seems simple enough, if you don’t have a clue how things work you’ll be lost before you know it. There are a couple of scans (ping scan, port scan, host scan, OS scan, stealth scan, and so on) you can do with Nmap and all of them call for console commands, which will require some level of technical expertise – or, at least, following throughout tutorials.
Customer support
Considering Nmap is freeware, it’s hardly a surprise there’s no customer support service working around the clock across several channels.
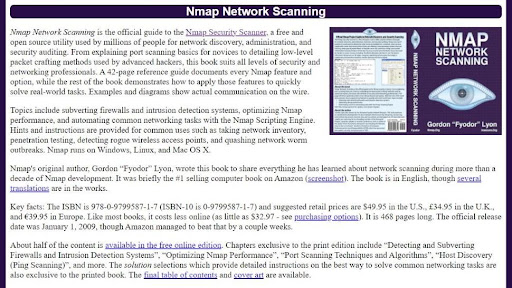
Fortunately for less tech-savvy users, there is a well-documented, cross-lingual knowledgebase that comprises up-to-date and easy-to-follow tutorials, whitepapers, man pages, and even an official book on Nmap scanning that’s available for free - however, you’re more than welcome to purchase the printed version of the book for $32.97.
Competition
If you’re looking for something like Nmap but simpler and somewhat concerned with scanning IPs, check out Angry IP Scanner. It covers most of the Nmap’s standard scanning capabilities but doesn’t dive into querying ports.
Another awesome (and outrageously obvious) alternative to Nmap is Zenmap since it’s an official GUI version of Nmap – it’s essentially the same as Nmap but with a bit more beginner-friendly approach due to GUI. Nevertheless, some people prefer to use Nmap without such a console and we’ll never understand why.
While OpenVAS is a far cry from a simple-to-use tool, in comparison with Nmap it looks almost beginner-friendly. Also, Nmap isn’t a vulnerability scanner (not without suitable scripts), and OpenVAS is, so if your main mission is to find weaknesses inside a system - OpenVAS is the way to go.
Final verdict
Nmap is a free, open-source utility utilized by millions of people across the world for network discovery and security auditing – and you can be one of them. Even its core set of features includes port scanning which is a swift way to discover any suspicious devices sneaking around your network.
However, on the downside, Nmap’s old-fashioned GUI could use some improvement, and Nmap itself would benefit from a more beginner-friendly approach.
- Check out our list for the best antivirus software
Sead is a seasoned freelance journalist based in Sarajevo, Bosnia and Herzegovina. He writes about IT (cloud, IoT, 5G, VPN) and cybersecurity (ransomware, data breaches, laws and regulations). In his career, spanning more than a decade, he’s written for numerous media outlets, including Al Jazeera Balkans. He’s also held several modules on content writing for Represent Communications.





 Become a TechRadar Insider
Become a TechRadar Insider



