Software & Services
Latest about Software & Services

Best IP address tools of 2025
By Benedict Collins last updated
Updated We list the best IP address tools, to make it simple and easy to better manage networks.

The best Adobe Portfolio alternatives 2025
By Alexis James last updated
Updated We list the best Adobe Portfolio alternatives, to make it simple and easy to better manage your images.

Best translation software of 2025
By Will Dalton last updated
Updated We list the best translation software, to make it simple and easy to better connect with global audiences.

Best free WinZip alternative of 2025
By Daryl Baxter last updated
Updated We list the best free WinZip alternatives, to make it simple and easy to manage compressed files without having to buy a software license.

The best photo recovery apps of 2025
By Mike Jennings last updated
We list the best photo recovery apps, to make it simple and easy to restore missing images and other graphics files.
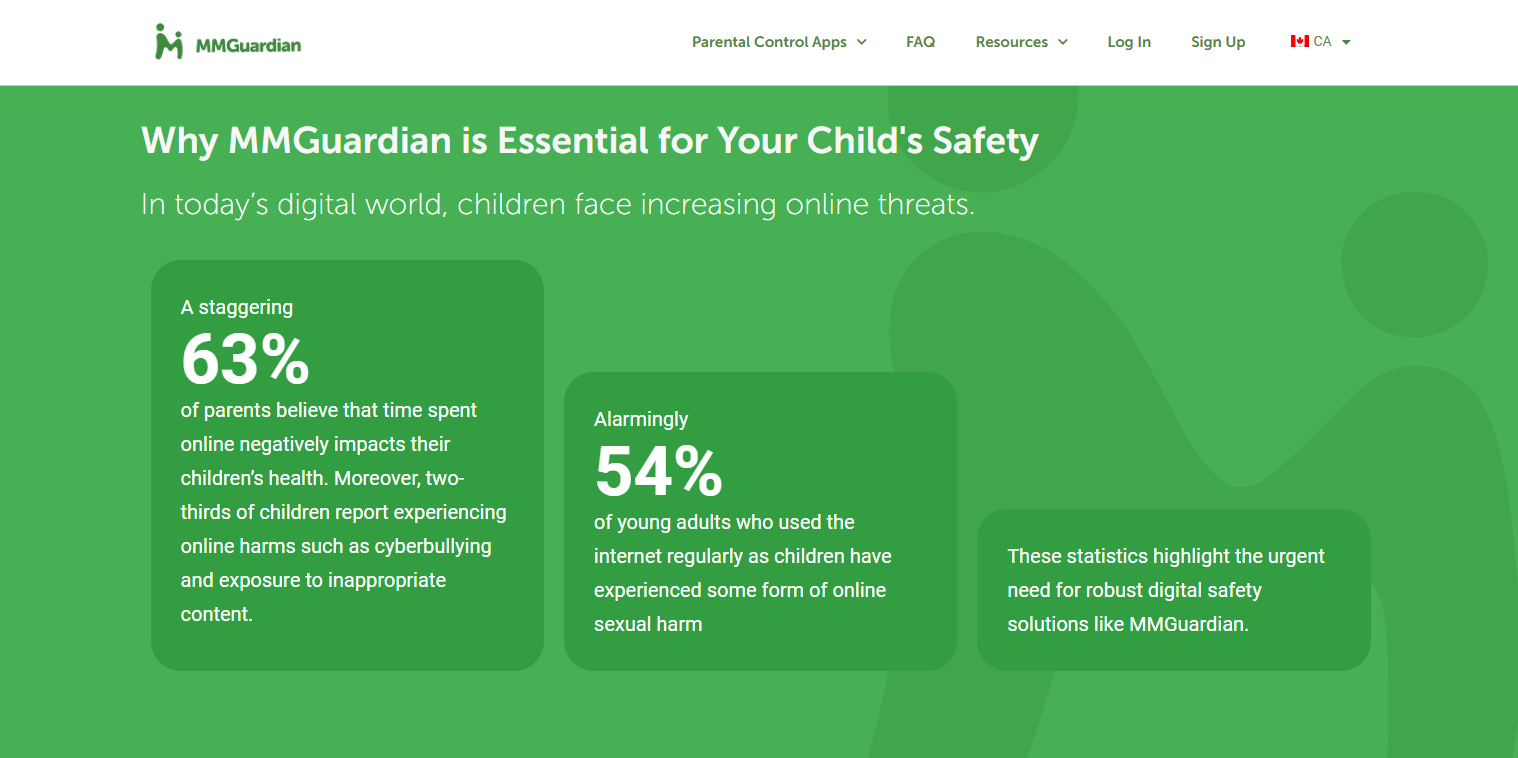
Parental Control Kroha review
By Mike Jennings last updated
Kroha handles call and SMS monitoring well, but if you need more than that, you're better off elsewhere.

mSpy parental control software review
By Mike Jennings last updated
mSpy provides excellent monitoring but you'll likely find a cheaper solution with more features elsewhere.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!