Hackers are abusing a disputed vulnerability to launch attacks on Linux machines
Users told to follow recommended security practises to mitigate risks

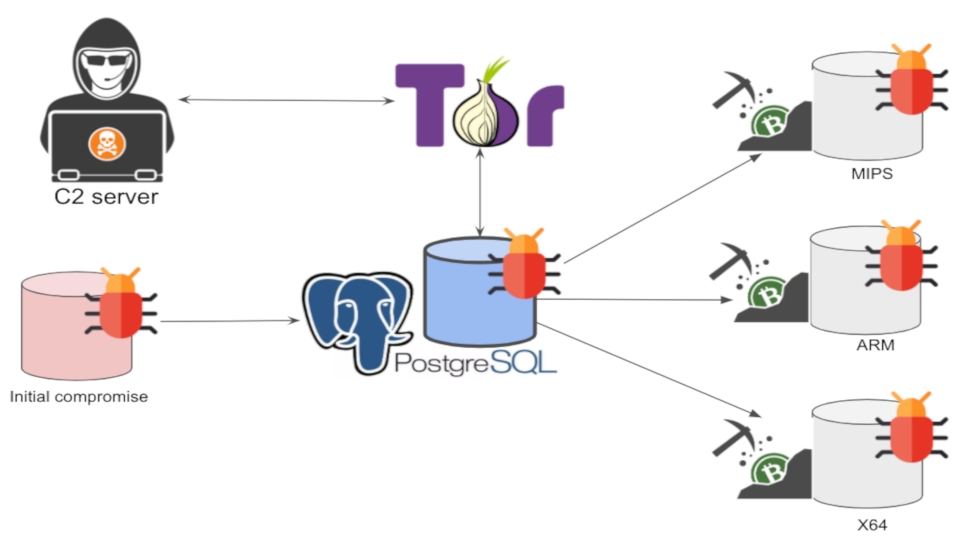
Security researchers from Palo Alto Networks have discovered a new botnet that targets misconfigured PostgreSQL databases running on Linux servers to install a cryptocurrency miner.
Named PgMiner by the researchers, the bot performs brute-force attacks against PostgreSQL databases, and exploits its disputed remote code execution (RCE) ability to mine the Monero cryptocurrency.
PostgreSQL is one of the most popular open-source relational database management systems (RDBMS). Although it was first released over two decades ago, the database is still ranked as the fourth most popular database by DB-Engines as of December 2020.
Article continues below- We've also highlighted the best endpoint protection software
- Here are some of the best malware removal software
- Stay safe with these best ransomware protection tools
Exploits human error
“We believe PGMiner is the first cryptocurrency mining botnet that is delivered via PostgreSQL,” note the Palo Alto Networks Unit42 researchers.
The researchers explain that PGMiner hunts for PostgreSQL installations whose administrators have forgotten to disable the default ‘postgres’ administrator user account. It then brute-forces its way to the account’s password, before exploiting PostgreSQL’s controversial copy from program feature to start mining.
The copy from program feature was introduced in PostgreSQL v9.3 back in 2013 and allows local and remote superusers to run shell scripts directly on the server.
Security researchers dubbed this feature a vulnerability since it could be used to launch attacks from compromised databases. However, the PostgreSQL community disputed calling it a vulnerability since it could only be exploited on misconfigured installations.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
PGMiner has proved them both right.
While the Unit42 researchers only found evidence of PGMiner targeting Linux servers, they argue the malware could theoretically be made to attack other platforms since PostgreSQL runs on Windows and macOS as well.
- These are the best antivirus software
Via: Palo Alto Networks
With almost two decades of writing and reporting on Linux, Mayank Sharma would like everyone to think he’s TechRadar Pro’s expert on the topic. Of course, he’s just as interested in other computing topics, particularly cybersecurity, cloud, containers, and coding.

 Become a TechRadar Insider
Become a TechRadar Insider







