
We may love our Linux boxes, but most of us will at some point need to co-exist on a network with Windows machines, and will know Samba as the thing that enables sharing filesystems between Linux and Windows.
But it does much more than that and, with version 4, is fully compatible with Microsoft's Active Directory.
This is a big thing. Samba has long been able to act as a Windows NT 4.0 Domain Controller, or join an existing Windows NT 4.0 Domain but, with the release of Windows 2000, Microsoft started moving away from NT Domain controllers to their new Active Directory, widening the gap between the Linux and Windows ecosystems.
Samba version 4 provides the long-awaited remedy to this issue by being fully compatible with Active Directory. It fully implements the Active Directory domain controller functionality, making it an effective replacement for the equivalent functions in Microsoft's Windows Server product line.
Samba is an open source implementation of the Server Message Block, or SMB, protocol. It is an application-layer network protocol that was originally developed by IBM to provide shared access to files and printers. Microsoft extended its implementation of SMB to support authentication using its own NT LAN Manager (NTLM) and, later, NTLMv2 protocols.
It called this implementation the Common Internet File System, or CIFS. Further extensions, including support for symbolic links, were released as SMB2 with Windows Vista.
Samba has supported SMB2 since version 3.6. Microsoft introduced SMB2.1 with Windows 7 and SMB3 with Windows 8. It calls the differing versions of the protocol "dialects", so CIFS and SMB2 are dialects of the SMB protocol.
Get daily insight, inspiration and deals in your inbox
Get the hottest deals available in your inbox plus news, reviews, opinion, analysis and more from the TechRadar team.
Whilst these dialects are proprietary, their specifications are publicly available: one of the outcomes of Microsoft's settlement with the European Courts in 2004 was the release of full documentation for network authentication with Active Directory. This led to the development of version 4 of Samba, with Microsoft itself being involved in the testing.
Active Directory (or AD, as it is known) is a central location for the administration of networked Windows computers. Servers that run Active Directory are called domain controllers. An Active Directory domain controller (which we'll abbreviate to ADDC) authenticates and authorises all users and computers in a Windows network, assigning and enforcing security policies for all computers and installing or updating software. For example, when a user logs in to a computer that is part of a Windows domain, the ADDC checks the submitted password and determines whether the user is a system administrator or normal user.
AD makes use of Lightweight Directory Access Protocol (LDAP) versions 2 and 3, Kerberos and DNS. Samba uses its own LDAP implementation called ldb; it does not support using OpenLDAP for Active Directory.
So there are now two ways to use Samba: one is to use it how it's always been used ('classic' Samba), which can either operate as a domain member or standalone, and is all that you need to set up basic shares. The other way is to use Samba as a fully-fledged ADDC.
The way you use Samba will depend on your needs, but the first thing that needs to be done is to install it. Most distributions should have it in their repositories, although Samba 3.6 may still be the default option. The other option is to build it from source, downloaded from www.samba.org/samba/download.
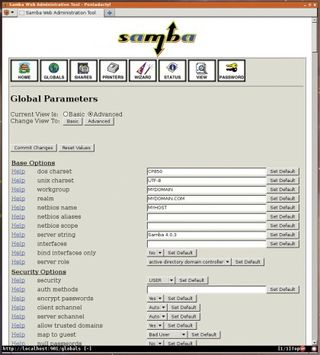
Once installed, Samba's configuration file is called smb.conf, and will normally be found in a sub-directory, like /etc/samba. The simplest configuration is for a standalone public share:
[global]
server string = Samba Server Version
%v
# Treat unknown users as a guest (where permitted)
security = user
map to guest = Bad User
[tmp]
path = /tmp
read only = No
browsable = Yes
guest ok = Yes
force user = nobody
force group = nobody
create mask = 0755
directory mask = 0755
Most Popular
