Sponsor Content Created With Dell
How ML-driven threat detection revolutionizes backup and recovery

TL;DR
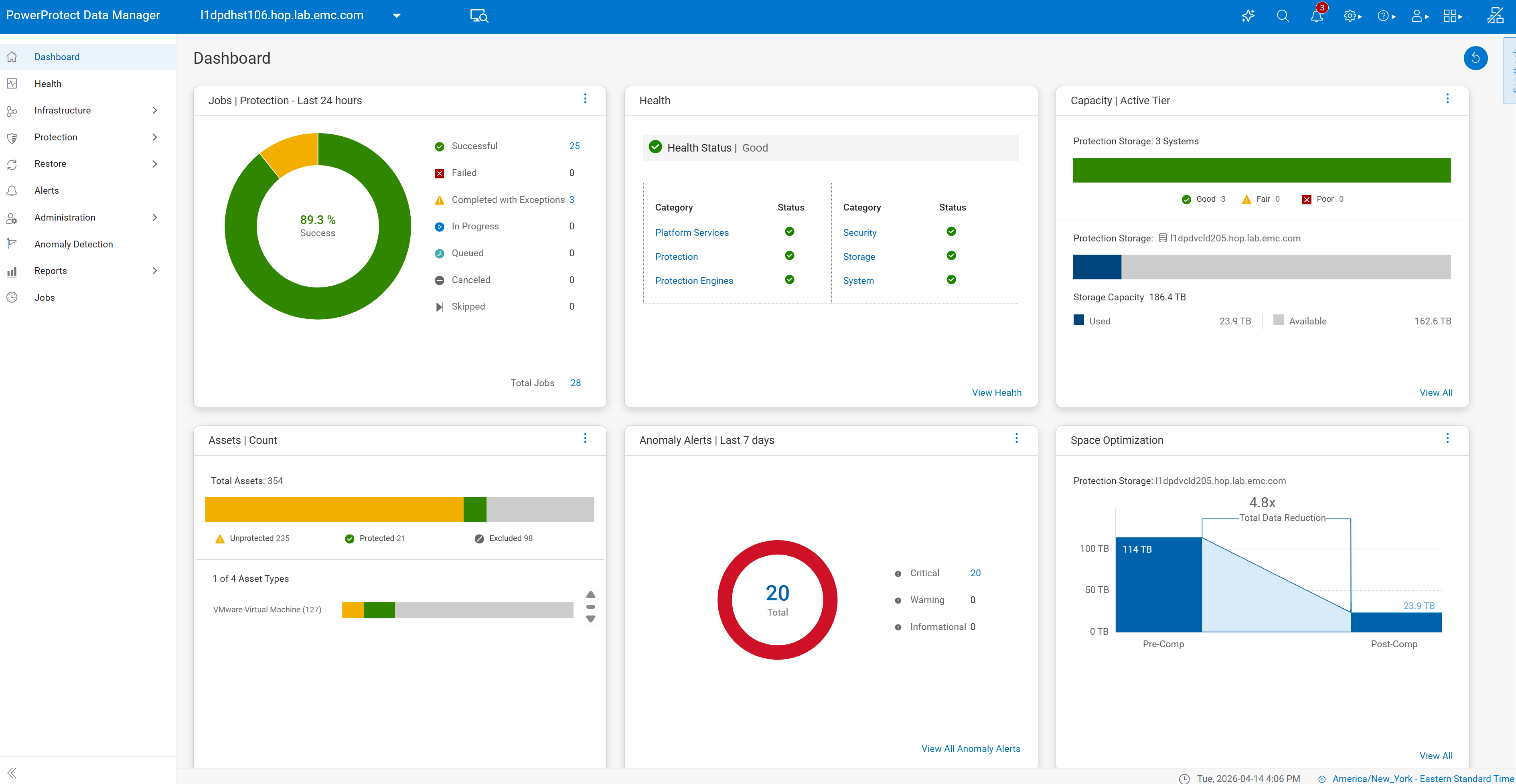
- Dell PowerProtect Data Manager uses AI to detect anomalous backup activity, signaling potential data threats
- Early detection empowers administrators to respond quickly to malware and ransomware attacks
- Automatic restore-point detection helps businesses recover from a breach with minimal disruption
- Orchestrated recovery ensures systems can roll back smoothly to a trusted state
- Policy-based protection also covers on-premises, hybrid, and cloud-native workflows
Cyber-attacks don’t just affect live data. In many breaches, the damage quietly spreads into backups long before it’s discovered. Encrypted or corrupted files can go unnoticed for weeks, or months, and become incorporated into backup sets. IBM’s “Cost of a Data Breach 2025” report found that it takes an average of 241 days to identify and contain an active breach across all industries.
The result? Wasted storage space, a false sense of security and significant disruption when attempting to restore data and workflows.
Dell PowerProtect Data Manager is more than a traditional backup tool, it’s an active defense against hidden data corruption. Using ML-based analysis, it can raise the alarm as soon as it encounters suspected bad data, providing an early warning for administrators and helping businesses to quickly roll back any unwanted changes.
Because the platform uses pattern matching against thousands of known ransomware and behavior analysis of backup metadata, rather than focusing on content, it can protect a wide range of workloads from conventional documents to AI datasets, virtual machines and cloud-native data stores.
Protecting backup data with early detection of cyber-threats
PowerProtect Data Manager uses ML-assisted analysis to spot anomalous activity such as a sudden increase in the number of changed files that are queued for backup. This allows it to flag suspicious behaviour at the earliest opportunity.
Traditional backup tools, by contrast, will simply back up all files that meet specified criteria – meaning that multiple bad restore points could be created before administrators become aware of an issue. It could even be that a breach isn’t spotted until a recovery attempt fails.
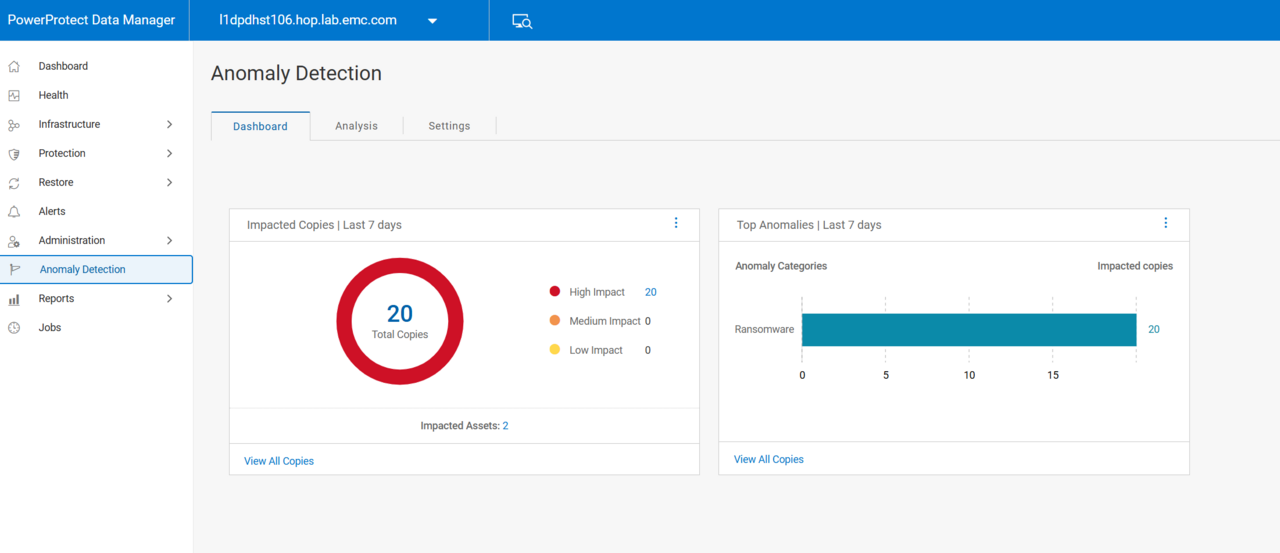
Data Manager’s Anomaly Dashboard lets administrators explore anomaly alerts, examine flagged data sets and mark false positives or confirmed threats – enabling a quick and reliable response to suspected corruption.
Spotting anomalies and hidden corruption in backup data
Data Manager doesn’t just monitor backup activity patterns; it tracks anomalies such as large numbers of files suddenly changing at once, or growing, or being renamed. The system can even spot the telltale signature of encrypted data inside files, enabling it to warn of suspected ransomware activity.
This is a powerful defense against ransomware attacks. Typically, malicious encryption begins silently, before administrators are aware of an infection. Flagging suspected corruption at the earliest juncture helps to ensure that businesses get the earliest possible warning of a compromise, and don’t end up unwittingly relying on corrupted backups.
Ensuring recovery starts from the right restore point
When data corruption is confirmed, PowerProtect flags the compromised data. It can be quarantined to prevent its use as a recovery point, which allows for a clean recovery point to be determined and uncorrupted data to be restored. This means that, in the event of a ransomware attack or a major data corruption incident, administrators can get on with recovering data, without spending time searching through backup points to find good, recoverable data.
Prompt action also makes it more likely that key data will be recoverable – Infrascale has reported that just 13% of organisations are able to fully recover their data after a ransomware attack. And by identifying the last clean restore point, PowerProtect Data Manager helps administrators establish the timescale of an attack, and track its progression.
Restoring systems faster with Orchestrated recovery
Dell PowerProtect Data Manager doesn’t stop at detection. It orchestrates recovery so systems and applications are restored in the correct sequence, reducing dependency errors and downtime.
For example, Data Manager can restore VMs with Recovery Orchestration and then use application-aware capabilities to restore business applications and services running on the VM. Management policies can define which workloads or systems should be restored as a priority, to keep disruption to an absolute minimum.
After recovery, the Data Manager software can verify that the backed-up data has been successfully restored, helping administrators confirm a return to the pre-infection or pre-corruption state.
Capability | Traditional backup | Dell PowerProtect Data Manager |
Threat detection | None | ML-assisted anomaly detection |
Restore point identification | Manual | ML-assisted |
File recovery | Manual | Orchestrated |
Workflow recovery | Manual | Orchestrated, policy-driven |
Cyber-resilience | Passive | Early warning and orchestrated recovery |
Multi-platform, multi-architecture support for all-round protection
In addition to on-premises files, data and VMs, Dell PowerProtect Data Manager works with hybrid and multi-cloud architectures, extending the same policy-based backup and threat detection to cloud-hosted virtual machines and Kubernetes clusters. It integrates with PowerProtect Data Domain, Dell’s backup storage solution that’s designed to efficiently handle large backup sets with high data throughput and integrated deduplication. And the most critical data can be protected via integration with PowerProtect Cyber Recovery, which keeps safe copies of key files isolated from the main network, for maximum resilience against ransomware.

For any business that runs on data, Dell PowerProtect Data Manager is an invaluable tool that provides active protection and fast, reliable recovery if a breach does occur. Thanks to ML-driven threat detection, it turns backup into a key pillar of your cyber-resilience strategy.
If you think PowerProtect is the right storage solution for your business, find out more on the Dell website: US readers click here and CA readers here.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!

 Become a TechRadar Insider
Become a TechRadar Insider






