Everything we know about Lapsus$ and Okta so far
More details emerge about hacking collective Lapsus$ and its latest breach

Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
You are now subscribed
Your newsletter sign-up was successful
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
It has been a busy week for hacking and extortion collective Lapsus$. It first leaked what it claimed to be employee account information from LG Electronics, as well as source code for a variety of Microsoft products.
A few hours later, the group also released screenshots indicating it had breached identity and access management company Okta. News of the potential breach spread quickly online.
Okta provides a single sign-on service for large organizations that allows employees to log in to multiple systems without requiring a different password for each one. An Okta hack could have potentially severe implications for customers.
Article continues belowOkta's response
Okta published a preliminary statement on Tuesday morning, indicating that the screenshots Lapsus$ released came from "an attempt to compromise the account of a third party customer support engineer working for one of our subprocessors" that occurred in January this year.
A second statement from David Bradley, Chief Security Officer at Okta, provided more details about the "unsuccessful attempt" to breach the support engineer's account.
While reassuring customers that "the Okta service has not been breached and remains fully operational", he also admitted that a forensic investigation found "there was a five-day window of time between January 16-21, 2022, where an attacker had access to a support engineer's laptop". Bradley insisted, however, that "[t]he potential impact to Okta customers is limited to the access that support engineers have", noting in particular that the hacking group cannot download customer data and does not have access to passwords.
Independent security researcher Bill Demirkapi provided further details to TechRadar Pro via email. He explained that the third-party support engineer appeared to work for SYKES Enterprises, Inc, now confirmed by Okta, and that, "using the access this support staff had, Lapsus$ was able to breach Okta's internal Slack, Jira, and backend administrative access panel used to assist customers". He added that, "at this time, it does not appear like Lapsus$ still has access to Okta's environment."
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
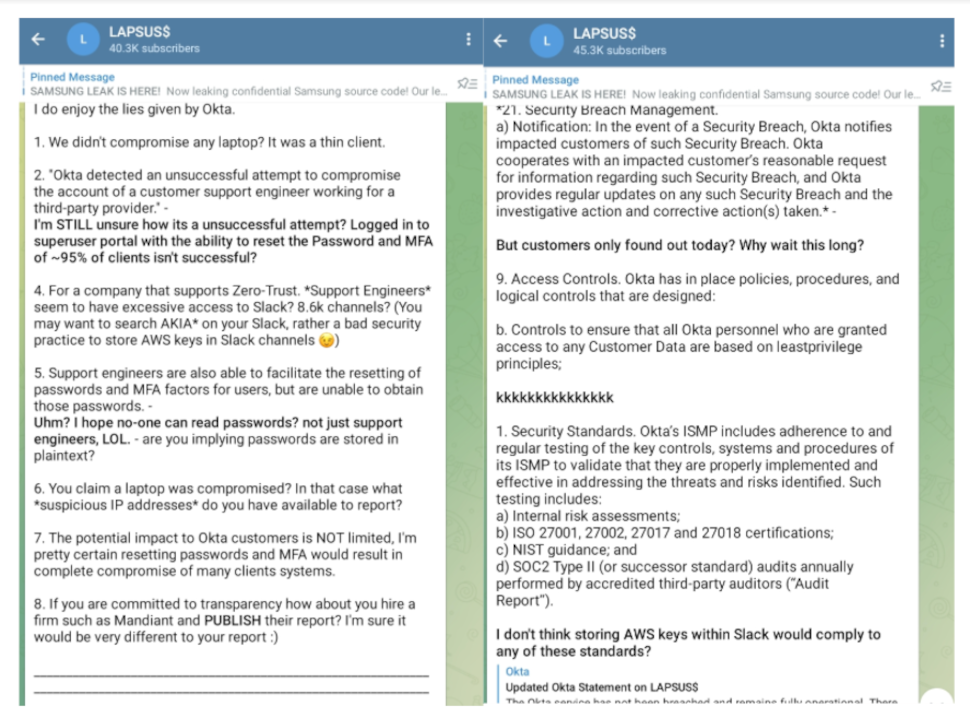
On Tuesday afternoon, Lapsus$ responded to Bradley’s statement in its Telegram channel, taking issue with his characterization of the attack as “unsuccessful". Lapsus$ also claimed that Okta had been storing AWS keys in Slack and called the company out for waiting so long to notify their users about the January incident.
Bradley has since acknowledged that "a small percentage of customers - approximately 2.5% [366 companies] - have potentially been impacted" by the incident and may have had their data "viewed or acted upon", though he continues to insist “there are no corrective actions our customers need to take".
In a separate post, Bradley laid out a timeline for the incident and addressed Lapsus$'s earlier reference to a "superuser" portal, shutting down claims that this gave the group "god-like access" to customer accounts. Instead, Bradley clarified that the superuser portal “is an application built with least privilege in mind to ensure that support engineers are granted only the specific access they require to perform their roles".
Okta has faced criticism, both from Lapsus$ and the security industry, for not disclosing the January incident sooner. Unsurprisingly, the breach has made investors nervous, leading to a drop in Okta's stock price, as well as a downgrade from Raymond James Equity Research.
Who is Lapsus$?
Despite the chaos its members caused this week, Lapsus$ is relatively new to the cybercrime scene. The hacking collective first emerged at the end of last year, but has already breached big names, including Microsoft, Nvidia, Samsung and Ubisoft.
On Tuesday, Microsoft published a report about Lapsus$, noting the group is unconventional, because it broadcasts its activities on social media and openly recruits employees willing to give them access to companies they want to hack.
While gaining the group online fans, Lapsus$’s social media presence also works to its detriment. Lapsus$ made the attack on Microsoft known on social media while it was taking place, which Microsoft said "escalated our action allowing our team to intervene and interrupt the actor mid-operation, limiting broader impact".
Bloomberg reported on Wednesday that two of Lapsus$’s members are thought to be teenagers, one living near Oxford in the UK and one in Brazil. The British teenager, known by the aliases "White" and "Breachbase", was identified by cybersecurity researchers as early as mid-2021 after leaving a trail of information about himself online. He was also doxxed by other hackers, who claim he has nearly $14 million in cryptocurrency.
On Thursday, the BBC reported that seven people between the ages of 16 and 21 had been arrested by London police as part of an investigation related to Lapsus$, though it’s not clear whether the teenagers mentioned by Bloomberg were among those arrested. The seven have since been released under investigation.
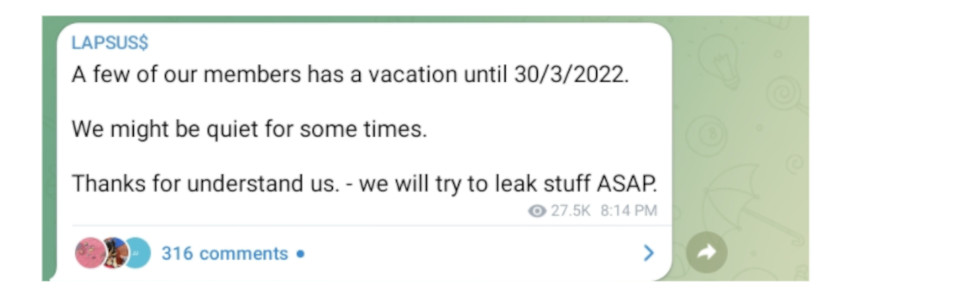
On Tuesday night, Lapsus$ announced that the group “might be quiet” for a while, since some of their members were going on “vacation until 30/3/2022". While the group promised to "try to leak stuff ASAP", in light of the recent arrests, the collective may be taking a longer break than intended.
Despite their youthfulness, the teen members of Lapsus$ are extremely knowledgeable. As Microsoft noted, Lapsus$ "understands the interconnected nature of identities and trust relationships in modern technology ecosystems and targets telecommunications, technology, IT services and support companies to leverage their access from one organization to access the partner or supplier organizations".
How companies can protect themselves
Microsoft’s report contained advice for companies about how to protect themselves against attacks from Lapsus$. The report noted that "multifactor authentication (MFA) is one of the primary lines of defense against" the hacking collective. But it also emphasized that insecure methods, such as SMS-based MFA, are not enough, since Lapsus$ has engaged in SIM-swapping attacks to gain access to SMS MFA codes.
As Lapsus$ often steals credentials via social engineering, Microsoft also recommended increasing employee awareness about these kinds of attacks. Other suggestions included making use of "modern authentication options" for VPNs, and ensuring incident response communication channels are "closely monitored for unauthorized attendees" in case Lapsus$ tries to sneak in.
In addition, Microsoft provided a collection of resources companies can use to help with "detecting, hunting, and responding to" attacks from Lapsus$ or groups mimicking the same methods.
- Here's our pick of the best endpoint protection software around
Rebecca Morris is a freelance writer based in Minnesota. She writes about tech, math and science.

 Become a TechRadar Insider
Become a TechRadar Insider







