Malicious GIFs could hijack your Microsoft Teams account
GIFs might lighten up your day, but not all are SFW
Sign up for breaking news, reviews, opinion, top tech deals, and more.
You are now subscribed
Your newsletter sign-up was successful
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
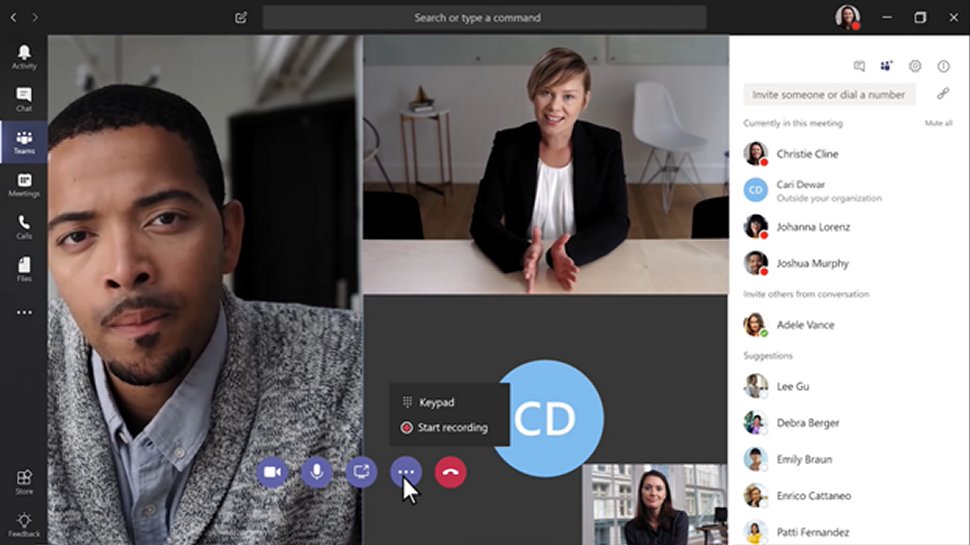
Security researchers have uncovered a vulnerability in video conferencing service Microsoft Teams that could allow hackers to scrape data and hijack accounts using malicious GIFs.
According to the report, the subdomain takeover vulnerability allows hackers to steal login credentials, take over accounts and further sow infected images - and eventually seize control of an organization’s entire account roster.
Discovered by US-based security firm CyberArk, the Microsoft Teams flaw affects both desktop and web browser clients. Reportedly, users do not have to share or interact with the GIF to be infected - only receive it.
Article continues below- Major Microsoft Teams update brings host of new features
- What is Microsoft Teams? How it works, tips and tricks and best alternatives
- Microsoft Teams doubles down on security advice
Microsoft Teams security flaw
In line with similar growth seen by its video conferencing rivals, Microsoft Teams surged to 44 million daily active users in mid-March as a result of coronavirus lockdown measures - a figure that is likely even higher at the time of writing.
Meteoric growth among video conferencing services has also attracted heightened attention from cybercriminals looking to take advantage of remote workers. As a result, market leading services such as Zoom have been left scrambling to shore up any potential chinks in their security armor.
The Microsoft Teams exploit discovered by CyberArk makes use of a quirk in the way the application handles image resources, such as GIFs. Each infected user can be converted into a “spreading point” and the malicious image can also be delivered to group channels, accelerating the rate of infection.
The capacity for a stealth-based approach makes this variety of attack especially potent - by the time the incident is detected, many (if not all) accounts could have been compromised.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
According to Geraint Williams, CISO at risk management firm GRCI, effective identity and access management can go a long way towards mitigating against attacks of this kind.
“With tools like Teams, it is so important to ensure that only approved and regulated users can access the platform and post in collaboration activities - it all boils down to having robust user access controls and strong authentication processes in place,” he told TechRadar Pro.
“It’s also crucial that you regularly attack these defences yourself so you can assess them for weak points...so you can simulate malicious insiders and identify the extent of the damage attackers can cause.”
Thankfully, it appears the Microsoft Teams flaw has not been actively abused by cybercriminals. In a written statement, Microsoft confirmed it had been alerted to the account takeover vulnerability and has since issued a fix.
"We addressed the issue and worked with the researcher under Coordinated Vulnerability Disclosure. While we have not seen any use of this technique in the wild, we have taken steps to keep our customers safe," said the firm.
- Here's our list of the best video conferencing software on the market

Joel Khalili is the News and Features Editor at TechRadar Pro, covering cybersecurity, data privacy, cloud, AI, blockchain, internet infrastructure, 5G, data storage and computing. He's responsible for curating our news content, as well as commissioning and producing features on the technologies that are transforming the way the world does business.
 Become a TechRadar Insider
Become a TechRadar Insider






