Worrying new hack attacks DDR3 memory
Rare hardware attack
Security researchers on Google's Project Zero initiative have discovered how to launch an attack that takes advantage of physical weaknesses in some types of DDR memory chips inside Intel-compatible PCs running Linux.
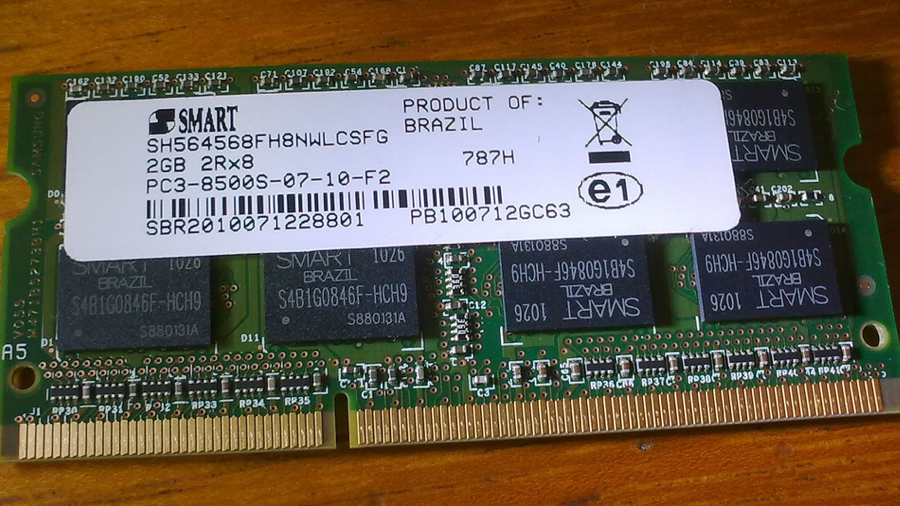
A blog post published earlier this week explained that the bit flipping technique flagged up last year has been used in a successful attack by researchers who were able to reverse the individual bits of data stored in DDR3 chip modules that are called DIMMs.
Bit flipping works when attackers repeatedly hammer small parts of the memory hundreds of thousands of times in just a few milliseconds. By hammering the two "aggressor" memory regions the attacker can then reverse one of more bits in the third "victim" region and exploit that to change the administrator privileges on the target PC.
It affects newer versions of DDR3 memory that are able to be exploited thanks to the shrinking size of silicon that makes it easier to trigger electronic interaction between neighbouring cells. By repeatedly accessing the location, as mentioned earlier, attackers can cause a leak in or out of the adjacent cells.
For now it's only local
The Project Zero researchers didn't detail the specific models of DDR3 that are prone to the attack and even though it sounds worrying the attack is currently only known to be local and thus decreases the scope for hackers wanting to launch attacks remotely.
Exploiting physical weaknesses in memory is still very rare and whilst repairing faulty software can be as simple as releasing a patch, replacing DDR memory may be the only way to solve the problems caused by this attack.
Via: Ars Technica, Project Zero
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!