Modern memory chips increasingly vulnerable to this physical hacking technique
Google calls on stakeholders to join the initiative to look for successful mitigations
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
You are now subscribed
Your newsletter sign-up was successful
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
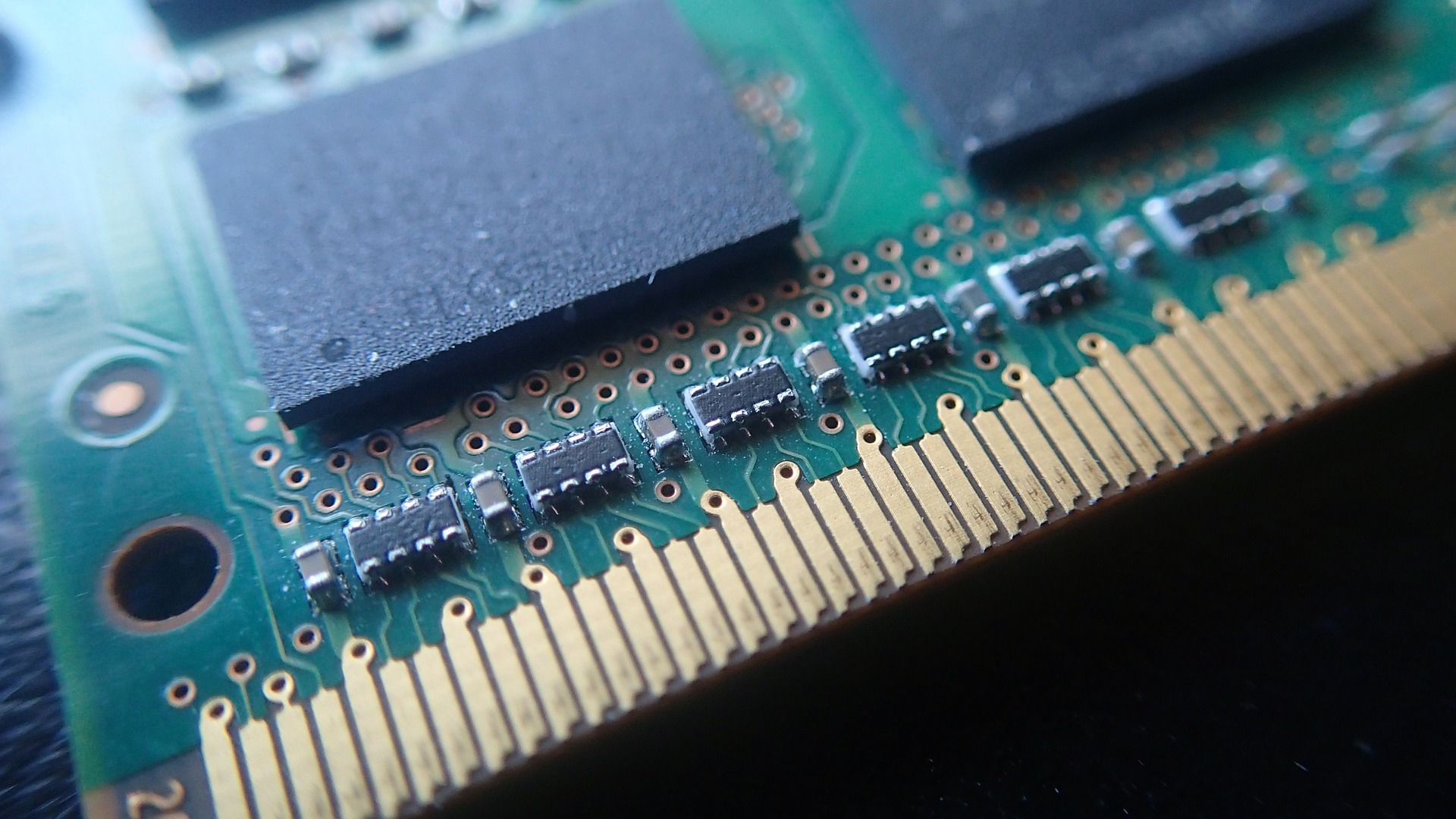
New research by Google engineers reveals that attacks based on the physical memory hacking technique known as Rowhammer are now more plausible thanks to recent improvements in the design of modern DRAM memory chips.
The Rowhammer hack works by manipulating the electrical charge in modern memory chips. The repeated hammering to one row of transistors results in the flipping of values in the adjacent rows.
First revealed in 2014, Google’s Project Zero released a working privilege-escalation exploit for Rowhammer in 2015. Since its revelation, DRAM manufacturers have added mitigations that keep an eye on rows of transistors for suspicious behavior.
Article continues belowWe're looking at how our readers use VPN for a forthcoming in-depth report. We'd love to hear your thoughts in the survey below. It won't take more than 60 seconds of your time.
- Protect your devices with these best antivirus software
- Here's our choice of the best malware removal software on the market
- These are the best ransomware protection tools
However, latest research by Google shows that as chips continue to get smaller with transistors packed in more closely together, hammering a particular row could in fact alter the values of not just the immediate neighbors, but of rows further away.
Half double attack
Google researchers refer to this new Rowhammer attack as Half-Double, even as they note that the technique wasn't viable on older generations of DRAM where transistor rows were placed farther apart than they are now.
“Traditionally, Rowhammer was understood to operate at a distance of one row: when a DRAM row is accessed repeatedly (the “aggressor”), bit flips were found only in the two adjacent rows (the “victims”). However, with Half-Double, we have observed Rowhammer effects propagating to rows beyond adjacent neighbors, albeit at a reduced strength,” write the researchers in Google’s Security blog.
The researchers also reveal that Google has been working with the JEDEC semiconductor engineering trade organization, and several other manufacturers from the industry to search for possible solutions for this new Rowhammer attack.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
In fact, the Google researchers refer to Rowhammer as a “substantial” challenge with far-reaching ramifications. They’ve shared the details of the new Rowhammer attack technique in a bid to call on stakeholders from the industry to join the effort to look for viable solutions.
- These are the best endpoint protection tools
Via Wired
With almost two decades of writing and reporting on Linux, Mayank Sharma would like everyone to think he’s TechRadar Pro’s expert on the topic. Of course, he’s just as interested in other computing topics, particularly cybersecurity, cloud, containers, and coding.

 Become a TechRadar Insider
Become a TechRadar Insider







