Beware - this WhatsApp feature might see your phone number end up in Google search results
WhatsApp numbers leaking into Google search results

Update: WhatsApp owner Facebook has now resolved the issue, which it was already working to fix before it was widely reported.
Users of WhatsApp’s Click to Chat feature could be sharing more than expected after personal phone numbers were found to be being exposed via public Google search results.
Click to Chat is a lesser-known WhatsApp facility that allows website visitors to converse with website operators via the messaging service. For example, if a visitor to an ecommerce site had a query about a listing, they could scan a QR code to be entered into a WhatsApp conversation with the relevant helpdesk.
Article continues belowHowever, according to researcher and bug-bounty hunter Athul Jayaram, utilizing this feature can land a user’s phone number in public search results, opening the door to all manner of scams and cyberattacks.
- Latest WhatsApp update brings a new world for business users
- Google Incognito mode is not as private as you might like to think
- Google could eliminate VPNs for millions with this new tool
WhatsApp data privacy
Messaging platform WhatsApp is renowned for its high data privacy standards, offering end-to-end encryption to all users. However, this latest discovery suggests personal data may not be as private as users might like to think.
Users’ numbers are being exposed by the WhatsApp-owned “wa.me” domain, which stores Click to Chat metadata in a URL string (e.g. https://wa.me/<WhatsApp number>). Because there is no measure in place to prevent search engines indexing this metadata, the numbers are in effect leaked into public search results.
“Your mobile number is visible in plain text in this URL, and anyone who gets hold of the URL can know your mobile number. You cannot revoke it,” explained Jayaram.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
“As individual phone numbers are leaked, an attacker can message them, call them, sell their phone numbers to marketers, spammers and scammers.”
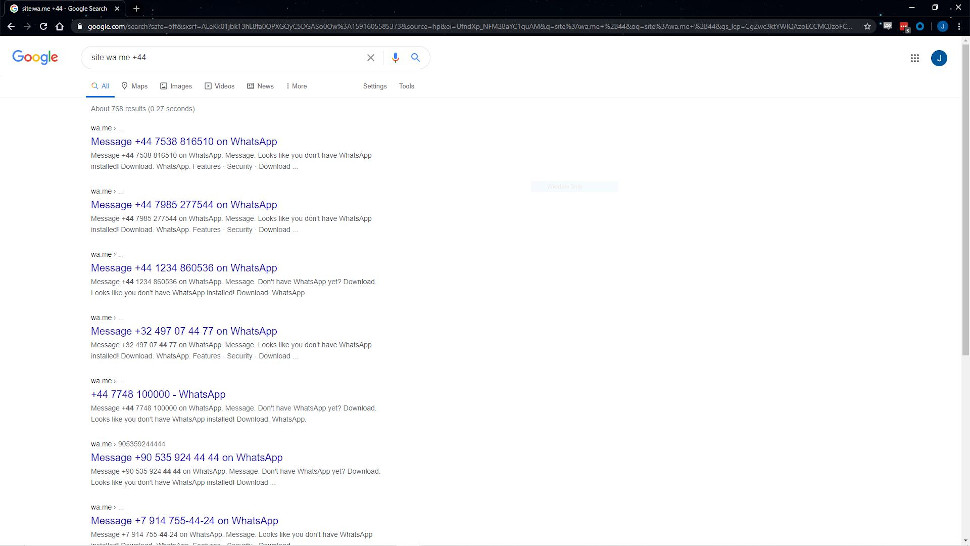
Scouring the domain via Google searches, Jayaram reportedly uncovered 300,000 WhatsApp numbers made public via this mechanism. Clicking through to the web page does not uncover the user’s full name, but does reveal their WhatsApp profile picture.
Having made the discovery on May 23, Jayaram subsequently reported the issue to WhatsApp owner Facebook through its bug-bounty scheme.
The application was dismissed, however, on the grounds that WhatsApp users have full oversight of the information attached to their profile that is made publicly available.
“While we appreciate this researcher’s report and value the time he took to share it with us, it did not qualify for a bounty since it merely contained a search engine index of URLs that WhatsApp users chose to make public,” said a WhatsApp spokesperson.
“All WhatsApp users, including businesses, can block unwanted messages with the tap of a button.”
Jayaram, however, believes the firm should take the disclosure more seriously, due to the scope of attacks the issue could facilitate.
“Today, your mobile number is linked to your Bitcoin wallets, Adhaar, bank accounts, UPI, credit cards…[allowing] an attacker to perform SIM card swapping and cloning attacks is another possibility,” he said.
- Here's our list of the best secure messaging apps on the market
Via Threatpost

Joel Khalili is the News and Features Editor at TechRadar Pro, covering cybersecurity, data privacy, cloud, AI, blockchain, internet infrastructure, 5G, data storage and computing. He's responsible for curating our news content, as well as commissioning and producing features on the technologies that are transforming the way the world does business.

 Become a TechRadar Insider
Become a TechRadar Insider






