Time for VPNs to go? Why zero trust is the way forward
Improving remote access with a more robust security model
Workplace policies continue to trend towards more flexible work, with over 58% of Americans reporting in a Spring 2022 survey that they had the opportunity to work from home at least one day per week. While this is excellent news for employee freedom, it also poses increased security challenges for companies.
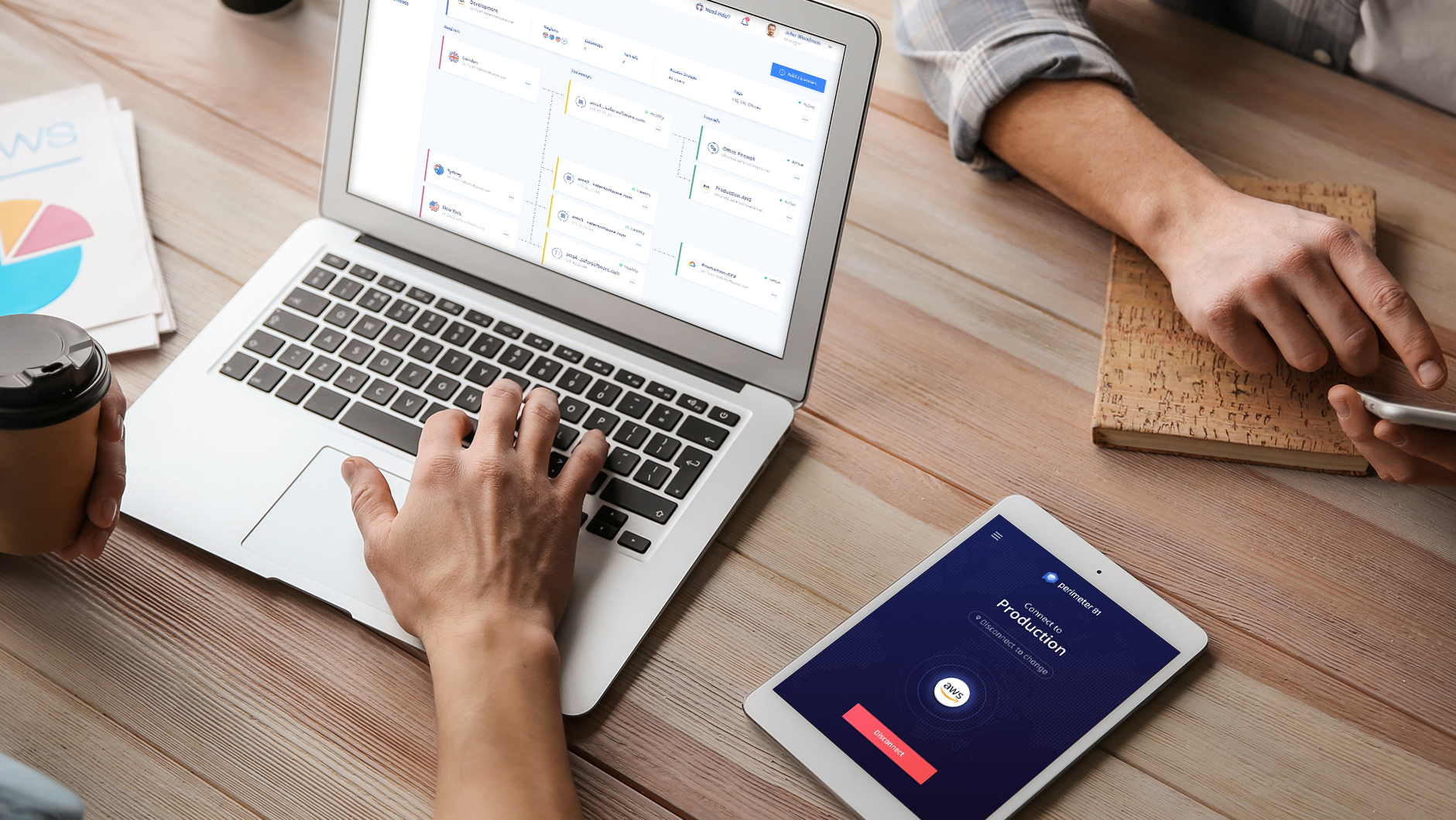
Remote workers are often required to access sensitive business resources over the internet, traditionally done with virtual private networks (VPNs). This outdated model is struggling to meet the demands of a massive remote workforce and is increasingly being replaced with Zero Trust solutions, such as Perimeter 81.
In this article, we look at why your company may wish to replace VPNs with a Zero Trust model.
The problem with the VPN trust model
VPNs have long been used to allow devices on different networks to communicate as if they were on the same network. By using a VPN over the internet, employees can connect to the company intranet and access all the resources as if their computer was plugged in there.
Crucially, VPNs don’t perform any additional security checks past the initial authentication, which is usually just a username and password. Once the remote device is authenticated, it continues to be trusted indefinitely. This is a security risk.
VPNs usually allow complete access to the company network for the remote user after they’ve been verified. With such broad access to all the applications and resources running on the network, a compromised remote machine could cause havoc to the business.
Another issue is that companies increasingly use cloud-based applications, storage, and other resources. You may want to leverage the power of enormous cloud-based resources from Amazon AWS, Microsoft Azure, and Google Cloud, but VPNs only offer perimeter-based security, protecting a local network.
Any solution that attempts to combine traditional VPNs with cloud technology will be clunky and difficult to maintain.
Employees often find VPNs frustrating to use. VPNs have limited authorization features, which means that creating and managing usernames and passwords for a large workforce can be tedious.
Hundreds of employees' network transactions must go through the VPN, which often causes a bottleneck. This can mean applications feel slow to respond and file transfers are slow.
Solution: The Zero Trust model
Zero Trust is a philosophy wherein no device or user is trusted automatically, no matter where they are located. This affects how your applications, network infrastructure, and company security policies are written and implemented.
The first striking change between using VPNs and Zero Trust is that users connected to the local company network are subject to the same security checks as everyone else. No longer are users or devices automatically considered trusted just because they are physically located in the building.
Zero Trust drops the policy of once verified, always trusted and replaces it with never trust, always verify. This means users and devices are constantly monitored for suspect behavior which may suggest the connection is compromised. For example, if the Zero Trust solution detects malware on a remote laptop, access to company assets will be immediately revoked until the issue is resolved.
VPNs can’t offer fine-grained controls over what each user can access on a network. Zero Trust solutions can. Instead of only offering general network-level security, Zero Trust can be used for more specific application-level protection.
With Zero Trust, users can be granted and denied access to particular applications. This is challenging to do with a VPN without putting applications on different networks. Advanced solutions can grant and deny requests to sections of an application based on user credentials. A low-level employee can be granted access to view select data but denied the ability to alter it, for instance.
Zero Trust and the cloud
Above, we discussed how the increased use of cloud-based resources in business doesn’t square well with the perimeter-based security model of VPNs. Zero Trust lays a solid foundation of never trust, always verify, so it doesn’t have the same issue.
With Zero Trust, every request for access to a company resource goes through a security middleman application, typically known as the broker. This broker checks to ensure the request is valid before handing off the request to the resource.
Notably, that resource doesn’t necessarily have to be on the company intranet. The broker could instead be the gatekeeper for an application on the cloud. This means that companies can put their resources on cloud servers instead of on the company intranet while maintaining a high level of security.
This offers many advantages. It becomes much easier to scale business applications, as you can leverage the immense power of public and private cloud networks as and when required. It can lower operating costs, as you no longer need so much hardware on-premises and the staff to maintain it. And, of course, it means better security for your vital business assets.
It's also great for your employees, as they can use one authentication and authorization system instead of keeping track of dozens of logins. The performance of applications can be drastically improved, as employees are no longer required to send all data back and forth through a VPN that often acts as a bottleneck.
Conclusion
An increasingly remote workforce and more reliance on cloud-based infrastructure mean the purely perimeter-based security model of VPNs is becoming outdated.
Zero Trust architecture offers more robust security and allows for more fine-grained control over what users can access. With the proper Zero Trust implementation, costs can be reduced, authentication is simpler for employees, and your critical business assets will be secure.
Find out more about Zero Trust Network Access (ZTNA), how to secure your network with Zero Trust, and why the US military is going all-in on Zero Trust.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
Richard brings over 20 years of website development, SEO, and marketing to the table. A graduate in Computer Science, Richard has lectured in Java programming and has built software for companies including Samsung and ASDA. Now, he writes for TechRadar, Tom's Guide, PC Gamer, and Creative Bloq.

 Become a TechRadar Insider
Become a TechRadar Insider







