Mac OS X vulnerable to new zero-day attack
Latest version of Yosemite affected
Sign up for breaking news, reviews, opinion, top tech deals, and more.
You are now subscribed
Your newsletter sign-up was successful
Apple Mac owners have come under attack from a zero-day vulnerability that has the potential to be exploited without needing the system password.
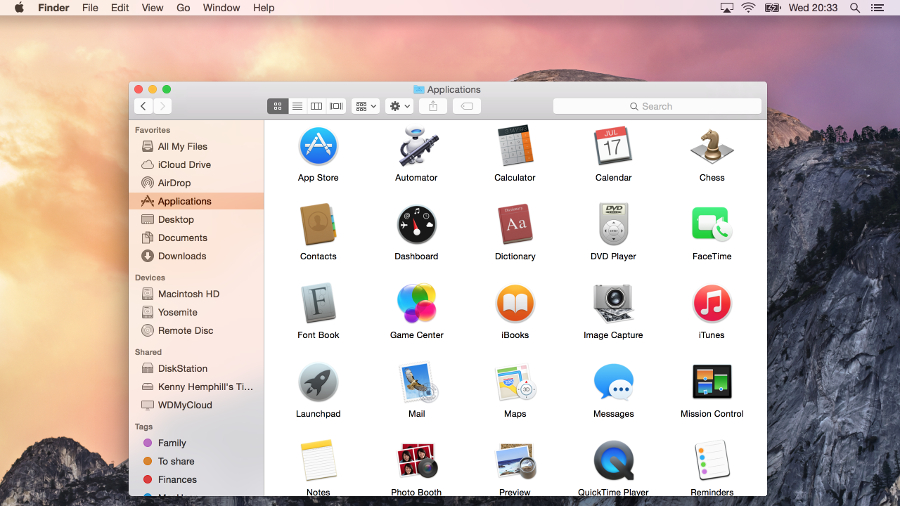
The major vulnerability affects the latest version of OS X Yosemite (10.10) after developers decided to add new error logging capabilities in OS X 10.10 and didn't use standard safeguards when doing so, according to Ars Technica.
Worryingly, researchers from Malwarebytes have found a new installer that is exploiting this problem to infect Macs with the VSearch adware and the worst part about it is that attackers don't need a password to gain root permissions via a Unix shell.
Article continues belowApple failed to patch up the flaw in the current 10.10.4 version of OS X, according to Stefan Esser, a security researcher, or a beta version of 10.10.5 tested by the same researcher, although the exploit doesn't work against 10.11, indicating Apple developers are working to eradicate it.
Wait for Apple's patch
Ridding your machine of the bug is currently quite difficult. The only fix right now comes in the form of a third-party patch produced by Esser himself and that in itself could come with a risk due to the fact it isn't made by Apple.
The best course of action is to hold fire until Apple issues a fix and in the mean time don't be alarmed as the exploit can only affect you if a faulty third-party program is present on your machine.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!