5 essential features your next email service needs to have
Safeguard your primary means of online communication from cyberattacks

Email is the most common form of online communication worldwide, with over 4 billion active users currently. Being the primary means of online communication also makes it the primary target of hackers and other malicious actors.
Email-based cyberattacks are increasing every day, and hackers constantly invent new ways to trick unsuspecting users into giving them sensitive information or money. Hence, the need for email security is as high as ever. Ignoring email security is doing a big disservice to yourself or your organization and could lead to hefty consequences down the road.
This article will explain the five security-related features that any email service you choose should have. Without these features, you’re taking significant security risks that could come home to roost later. They include:
Reader Offer: Start for free
Proton Mail is a very secure email solution with an intuitive interface that you'll likely enjoy using. It's one of the best secure email platforms available. Techradar editors love its sophisticated security features and excellent customer support. Start for free today.
Preferred partner (What does this mean?)

1. Encryption
Any worthwhile email provider must allow users to encrypt their messages to prevent unauthorized parties from snooping on them. Without encryption, you might as well be sending emails to the general public. Any email client you choose must have sophisticated encryption protocols to prevent users’ information from leaking to unauthorized parties.
The email service should let you encrypt messages as easily as possible. You shouldn’t have to jump through many hoops just to encrypt your emails; it should be direct and quick.
Below are some popular encryption protocols that email providers usually adopt.
Advanced Encryption Standard 256 (AES-256) was published by the U.S. National Institute of Standards and Technology in 2001. This algorithm uses 256-bit keys to encrypt and decrypt messages, making them impenetrable by a malicious actor.
To demonstrate how sophisticated this algorithm is, there are 2^256 possible key combinations a hacker can guess to brute force an encrypted message. That makes 115,792,089,237,316,195,423,570,985,008,687,907,853,269,984,665,640,564,039,457,584,007,913,129,639,936 attempts. Yes, you read that right.
An intending hacker would need a supercomputer to guess billions of possible combinations per second and still need over a billion years to go through all the possible combinations. The Sun might have run out of energy by then, and the Earth may not exist again, so no one bothers to brute force this algorithm using current technology.
AES-128 works the same way as AES-256, but with 128-bit keys. With 2^128 possible key combinations, virtually no one can brute force this algorithm to read encrypted emails.
PGP is an encryption protocol used to encrypt and decrypt emails, files, and directories transmitted over the web. It was created in 1991 by Phil Zimmermann, a prominent American computer scientist.
PGP supports key lengths of up to 4096 bits, making it even stronger than AES-256 or AES-128. It was so powerful at the time of its release that its creator, Zimmermann, was investigated for violating American arms export laws (at that time, encryption protocols using over 40 bits were considered munitions by the government).
Defending himself from the investigation, Zimmermann open-sourced the PGP protocol for anyone to build on. U.S. cryptography regulations liberalized shortly after, and the case against him was closed without any indictment.
Today, PGP is the most commonly used protocol for encrypting emails.
2. Backup
Data backup is an essential component of every security plan. Having the most sophisticated encryption protocols does not provide a 100% security guarantee. A human could be the weak link that causes your data to get stolen. Emails might also be lost due to data corruption or accidental deletion.
Backups protect your email data by storing them on external servers. This way, if the current server goes down, the email client can simply restore your data from another server, and you’ll experience no disruption.
Your email client should back up your data daily or weekly if the daily option is impossible. Frequent backups keep you prepared for any case of data loss.

3. Spam and Antivirus Filtering
Spam is the biggest problem on the internet. According to Statista, nearly half of emails sent daily constitute spam, presenting a major problem. Spammers come in many forms and are usually after unsuspecting people’s sensitive information or money.
An email service can’t exist in this era without advanced spam filters to protect users. Any service without spam filters exposes users to harm and is headed for backlash.
Ensure your email service has sophisticated filters to prevent spam from reaching your primary inbox. Popular email services like Gmail, Zoho Mail, Yahoo Mail, etc., have a lot of experience identifying and isolating spam. They apply machine learning and artificial intelligence algorithms to detect spam, especially in this age when spammers are catching up to manual techniques.
Of course, there can be false positives, so most email services shift suspected spam messages to a dedicated folder. You can enter the spam folder to see if any legitimate message was pushed there. If so, you can flag it as legitimate, and your email client will start accepting further messages from that email address.
Your email service should also be able to scan incoming emails for viruses and reject anyone it detects. Viruses usually come as malicious links the sender entices you to click or malicious files the sender wants to trick you into downloading. Your email client should scan links and attachments for viruses and reject or alert you to anyone it detects.
4. Multi-Factor Authentication
Multi-factor authentication implies requiring at least two modes of identification before granting access to an account. Your email client should allow you to use multi-factor authentication to secure your account. This way, someone won’t be able to access your email account even if they get your password. They must prove their identity by typing a code sent to your linked mobile phone number or another email address.
Fortunately, most mainstream email services support multi-factor authentication. Gmail is well-known for this feature, such that it has become a meme. When someone tries to log into your account on an unrecognized device, it immediately sends a prompt to the device you’re logged in on, asking you to authorize or reject the login attempt.

According to Microsoft, multi-factor authentication blocks 99.9% of account hacks, meaning it’s a big disservice to have it activated on your email address.
5. Anti-Phishing
Phishing is a social engineering attack that involves someone impersonating a trusted individual or organization to trick you into giving up sensitive information or sending money to them.
For example, someone might try to impersonate the CEO of your organization to trick you into giving up sensitive work passwords. The impersonation can be sophisticated, down to the same image, name, and conversation style as your CEO. Phishers use similar but not exact email addresses as the impersonated persons, and you might fall for it if you’re not careful. Take, for example, Frankl1n@gmail.com instead of Franklin@gmail.com; someone can easily overlook the spelling error, thinking it’s from the same address.
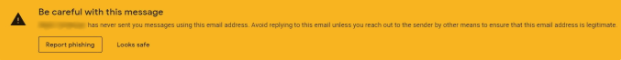
Your email service should have anti-phishing measures to prevent users from falling into this trap. For example, Gmail displays a yellow banner warning users whenever someone with a familiar name sends a message from an unfamiliar address. This banner alerts users to cross-check the email address to ensure it’s legitimate; many people might forget themselves and reply to a possible impersonator without it.
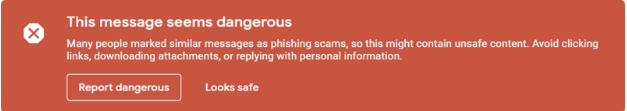
Sometimes, Gmail also shows a red banner warning that a message is likely a phishing scam. It places this warning when the message comes from an address people have previously reported for spam or phishing.
Any email service you choose should have advanced anti-phishing features similar to Gmail.
Final words
Cyberattacks are growing rapidly globally; according to McKinsey, they could cost $10.5 trillion in annual damages by 2025. It’s essential for any email service to protect users against cyberattacks as much as possible.
We have described 5 essential security features that the next email service you choose needs to have. Any email service without these features exposes you to potential harm and data loss that can be difficult to recover from.
Cyberattacks are becoming increasingly sophisticated, and email services must increase their sophistication to counter them. They must have advanced encryption, backup policies, spam and antivirus filtering, multi-factor authentication, and anti-phishing features.
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
Stefan has always been a lover of tech. He graduated with an MSc in geological engineering but soon discovered he had a knack for writing instead. So he decided to combine his newfound and life-long passions to become a technology writer. As a freelance content writer, Stefan can break down complex technological topics, making them easily digestible for the lay audience.

 Become a TechRadar Insider
Become a TechRadar Insider








