TechRadar's Sustainability Week 2024
All sustainability week coverage-

This Swedish startup made the tech behind the world’s first solar-powered headphones – here’s how it works
Meet the company making gadgets like headphones, speakers and remotes better for the planet with solar power.
-
-
 sustainability week
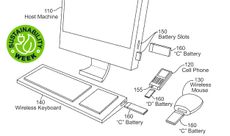
sustainability weekApple is exploring removable batteries for iOS devices – and I think AirPods need it most
Apple has filed a patent for an easy-to-replace battery standard for iPhones, tablets and keyboards – but AirPods aren't mentioned.
-

This company is making 35-year-old Game Boys look and work like new and now I'm hooked on Tetris
Retrospekt refurbs hundreds of Game Boys, Polaroid cameras, Sony Walkmans, and other gadgets to keep them in our hands and out of landfills.
-
 Sustainability Week
Sustainability WeekEbook vs paper: which reading medium is better for the environment?
If you’re environmentally conscious and love to read, is it time to ditch the dead-tree editions and switch to an ereader?
-

Rare's new eco-friendly studio building could potentially power more than 438,000 Xbox Series X consoles
Sea of Thieves developer, Rare, has built a brand new sustainability-focused studio building.
-
Explore TechRadar
Reviews
All reviews-

Asus ROG Strix Scope II RX review: a keyboard for the sophisticated gamer
A top-notch keyboard with great performance and a rich feature set, the only thing that lets the Asus ROG Strix Scope II RX down is its lackluster software suite.
-
-

Nikon Z 40mm f/2 review: this cheap, modern 'nifty forty' has been my everyday lens for over a year and it hasn't let me down
Nikon's cheapest prime is a cost-effective entry-point into the Z mount ecosystem and a great take on the 'Nifty Fifties' of old.
-

Instant Vortex 9-quart Air Fryer with VersaZone technology review: competent, but not flawless
The Instant Vortex Air Fryer with VersaZone technology serves up a large single cooking basket that can be divided into two for fuss-free air frying.
-

Withings ScanWatch Nova review: analog looks with exceptional digital brains
The Withings ScanWatch Nova 2 is an unassuming yet powerful smartwatch and health tracker.
-

JLab JBuds Lux ANC review: budget headphones that are all about that bass
The JLab JBuds Lux ANC are the brand's first 'luxury' over-ear headphones, which offer lots of bass but a few aches too.
-

iFi iDSD Diablo 2 review: the red DAC's more devilishly good second time around
As long as you’re not expecting some sort of sonic armageddon, the iFi iDSD Diablo 2 has an awful lot going for it.
-

Lenco L-3810 review: striking the perfect chord between analog and digital
Rely on Lenco to pile on the features, including the ability to digitize your vinyl collection, without letting costs get out of control.
-
How TechRadar tests

Product testing for the real world
You need to know that the device or service you’re about to spend money on works as advertised - and that it works in the real world.
- We test properly: objective and subjective testing
- We use experienced experts for our reviews
- We always offer 100 per cent unbiased, independent opinions
reviews
hours' testing
buying guides
Phones
All Phones-

Don't miss the Samsung Galaxy S23 Ultra for just $849 at Best Buy right now
Best Buy has cut more than $500 off the Samsung Galaxy S23 Ultra, bringing the price down to just $849.
-
-

Huge Samsung Galaxy S24 sale: get our best-rated Android phone for a record-low price
Best Buy is running a sale on the Samsung Galaxy S24 range with savings of up to $200 available on all handsets.
-

Holding out for a Samsung Galaxy S24 FE? You could be in for a long wait
The Samsung Galaxy S24 could be getting a Fan Edition released at the end of the year.
-

The iPhone 16 looks likely to ditch physical buttons after all
Apple will reportedly abandon all physical buttons on the iPhone 16 line.
-

Android 15 could have a new screen feature to keep you doomscrolling in bed
We've got a sneak preview of two more features heading our way with the Android 15 update later this year.
-

The Google Pixel 8a has leaked on video, providing our best look yet at the budget phone
A leaked video provides a clear look at the Google Pixel 8a in two colors, along with its retail box.
-

A full list of Samsung Galaxy Z Flip 6 and Z Fold 6 colors has leaked
A complete list of colors and storage capacities for both the Samsung Galaxy Z Fold 6 and Galaxy Z Flip 6 has been shared.
-
Laptops & Computing
All Laptops & Computing-

Meta’s massive OS announcement is more exciting than a Meta Quest 4 reveal, and VR will never be the same again
The surprise Meta Horizon OS announcement sets it up as VR’s Windows – and that’s both a great and terrible thing.
-
-

Asus ROG Strix Scope II RX review: a keyboard for the sophisticated gamer
A top-notch keyboard with great performance and a rich feature set, the only thing that lets the Asus ROG Strix Scope II RX down is its lackluster software suite.
-
 Sustainability Week 2024
Sustainability Week 2024Acer shows Apple how environmentalism is done with pledge to collect equivalent of 2.5 million plastic bottles with Plastic Bank partnership
Acer is one of the best companies for living up to its green pledges – and it’s now taking on plastic waste.
-

The best laptop deals in April 2024
Our expert guide to all the best laptop deals currently available.
-

AMD Radeon RX 7800 XT, one of the best midrange GPUs, is at its lowest price ever
One of the best midrange graphics cards on the market, the AMD Radeon RX 7800 XT, has reached an all-new low price.
-

Microsoft could add yet another advert into Windows 11 - and users are running out of patience
Microsoft tests user patience with ads in Windows 11, sparking debate over integration, privacy, and the future of the Windows user experience.
-
 Privacy at risk
Privacy at riskIs your phone tracking what you type?
Up to one billion Chinese-speaking people may have fallen victim to mass surveillance, a new report reveals. The culprit? Your phone's keyboard.
-
Apple
All Apple-
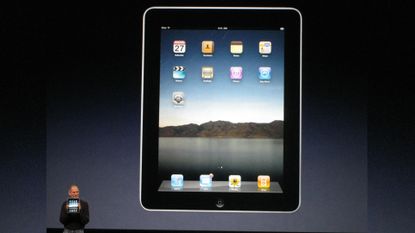
Steve Jobs was wrong about the post-PC era and the next batch of iPads should embrace this
The iPad changed everything but never quite how Steve Jobs imagined. Here's why the iPad didn't launch a post-PC era.
-
-

Apple could be playing it smart by waiting for its M4 chips before releasing a new Mac mini
If Apple ends up pushing back its Mac releases, starting with the Mac mini and other desktops, that would be its best idea in a long while.
-

The iPhone 16 looks likely to ditch physical buttons after all
Apple will reportedly abandon all physical buttons on the iPhone 16 line.
-

Apple TV Plus could soon take another big shot at soccer with landmark FIFA deal
FIFA is said to be in talks with Apple to launch a new high-profile soccer tournament, but the move has its critics.
-

It's time for AMD, Intel, and Nvidia to call a truce on the performance arms race and focus on sustainability and efficiency
AMD, Intel, and Nvidia have long been in a computing performance arms race that requires more power than we can sustain, so the big three need to shift their focus.
-
Streaming
All Streaming-
 Updated
UpdatedDeadpool and Wolverine: release date, trailers, confirmed cast, plot rumors, and more
Here's the scoop on Deadpool and Wolverine, the only Marvel movie set to debut in theaters this year.
-
-

Prime Video movie of the day: Asteroid City is Wes Anderson weirdness with a solid family story at its core
There's also a weird little alien guy, but maybe that's not such a surprise for a Wes movie.
-

Netflix movie of the day: Emily the Criminal is a super-tight crime thriller full of real bad decisions
Watch Aubrey Plaza get caught in a web of criminals.
-
 Updated
UpdatedThe best Paramount Plus shows: 21 terrific series to stream in April 2024
These are the best Paramount Plus shows to watch right now, including The Curse and Colin From Accounts.
-

Apple TV Plus could soon take another big shot at soccer with landmark FIFA deal
FIFA is said to be in talks with Apple to launch a new high-profile soccer tournament, but the move has its critics.
-
TVs
All TVs-
-

Best Buy is slashing prices on our best-rated OLED TVs - save over $1,000 while you can
Best Buy is having a huge sale on our best-rated OLED TVs, and I'm rounding up the best deals with over $1,000 from Samsung and LG.
-
 Updated
UpdatedThe best indoor TV antennas for 2024
These are the best indoor TV antennas for watching free TV channels at home.
-

How to buy a good secondhand TV, or make your old TV last longer
Buying a secondhand TV is a great way to save money and help prevent waste, but navigating it can be a bit of a minefield - we're here to help with that.
-

Brighter, low-energy OLEDs are going into production this year – but they won’t be coming to TVs just yet
New OLED displays could be twice as bright, twice as efficient and last three times longer but the best TVs won't be the first to see this new tech.
-

JMGO’s new 4K projector has a built-in gimbal so you can place it anywhere in your home
The new JMGO N1 Ultra promises to be the perfect projector for pretty much any space.
-

New Google TV 4K streaming stick tipped to land soon – and it could come with a new remote
Nearly four years after the Chromecast with Google TV 4K launched, there are rumors that a new one could launch soon.
-
 Hot deals
Hot dealsThe cheapest OLED TV deals and sales for April 2024
Your guide to the best OLED TV deals with incredible sales from brands like Sony, LG, and more.
-
Audio
All Audio-
-

Soundcore's new sports earbuds offer a Powerbeats Pro-style customizable secure fit for a fraction of the price
The Sport X20 specializes in customization as you can adjust the hook to fit your ear and tweak its audio output.
-
 TechRadar Deals
TechRadar DealsBest Apple Memorial Day sales 2024: date and deals to expect
Your guide to this year's Memorial Day Apple sales event, with key information such as the date and deals to expect.
-

The best wireless earbuds 2024
Here are our picks of the best wireless earbuds for Android, for iPhone, or anything else you want to connect them to.
-

This Android phone for audiophiles offers a hi-res DAC, balanced output and 3.5mm jack – plus a cool cyberpunk look that puts Google and OnePlus to shame
Stylish audio brand Moondrop’s first phone is more of a hi-res digital audio player with OnePlus and Google Pixel features.
-

Sonos' new app is a smarter, slicker music center that's perfect for, say, a pair of headphones
The next-gen Sonos app aims to deliver all your favorite audio in one smart home screen.
-

This Swedish startup made the tech behind the world’s first solar-powered headphones – here’s how it works
Meet the company making gadgets like headphones, speakers and remotes better for the planet with solar power.
-

Beats tipped to launch a new Bluetooth speaker after LeBron James flaunts mysterious device
LeBron James appears to have a Beats speaker that hasn't even been announced yet.
-
Health & Fitness
All Health & Fitness-
-

OnePlus Watch 2 Nordic Blue is the Wear OS dive watch I’ve been waiting for
OnePlus Watch 2 gets a dive watch makeover reminiscent of the Samsung Galaxy Watch 6 Classic.
-

Leaked Samsung Galaxy Ring model numbers hint at size options
We may have just learned some of the model numbers that the Samsung Galaxy Ring is going to be coming in.
-

Withings ScanWatch Nova review: analog looks with exceptional digital brains
The Withings ScanWatch Nova 2 is an unassuming yet powerful smartwatch and health tracker.
-
Cameras
All Cameras-
-

It’s finally happened: Canon opens up its RF-mount to Sigma and Tamron lenses
Six Sigma DC DN Contemporary lenses for Canon's APS-C cameras like the EOS R7 are on the way in 2024, and one from Tamron.
-

Nikon Z 40mm f/2 review: this cheap, modern 'nifty forty' has been my everyday lens for over a year and it hasn't let me down
Nikon's cheapest prime is a cost-effective entry-point into the Z mount ecosystem and a great take on the 'Nifty Fifties' of old.
-

'It’s nothing to do with photography' – Sony World Photography Award winners tell us their mixed feelings about AI
We asked Sony World Photography Award winners if AI-generated images have a place in photo competitions and how organizers should approach the tech. Here’s what they said.
-

Missed out on the Fujifilm X100VI? New leak suggests the next best thing could land soon
A new leak suggests that a Fujifilm X-T50 could launch soon – here's why it could be good alternative to the popular X100VI.
-
Home
All Home-
-

Instant Vortex 9-quart Air Fryer with VersaZone technology review: competent, but not flawless
The Instant Vortex Air Fryer with VersaZone technology serves up a large single cooking basket that can be divided into two for fuss-free air frying.
-

I tried Dyson's CleanTrace app, and it's the most fun you can have with a vacuum cleaner
Dyson's CleanTrace AR app turns vacuuming into a game – and it's a hugely satisfying one.
-

Samsung’s new energy-efficient appliances use AI to offer huge savings
Saving the planet with the power of smart bubbles
-

Cuisinart's soft serve sundae station is like a Pizza Hut Ice Cream Factory in miniature
The Cuisinart Soft Serve Ice Cream Maker delivers perfect ice cream in 20 minutes, and looks adorable while doing so.
-
Buying guides
All Buying Guides-

The best wireless earbuds 2024
Here are our picks of the best wireless earbuds for Android, for iPhone, or anything else you want to connect them to.
-
-
 Updated
UpdatedThe best indoor TV antennas for 2024
These are the best indoor TV antennas for watching free TV channels at home.
-
 Updated
UpdatedThe best Chromebook 2024
The best Chromebook can be a great alternative to MacBooks and Windows laptops.
-
 Updated
UpdatedThe Best Bird Feeder Camera 2024
If you want to see which feathered friends are visiting your garden, we've rounded up best bird feeder cameras for you
-
 Updated
UpdatedThe best Hulu movies: 26 great films to stream in April 2024
The best Hulu movies right now, including Wonder Woman, Hellboy and The Fifth Element.
-
 Updated
UpdatedThe best 4K graphics card of 2024: top options for gamers and creatives
Whether you’re looking to game in Ultra HD or looking to push a creative project forward, the best 4K graphics cards are up to the task.
-

The best computer 2024
Tired of your chunky old desktop? It might be time to get yourself one of the best computers, handpicked by our PC experts.
-
Why we're experts

We care passionately about tech
The TechRadar team has a life-long passion for the latest innovations – over 300 years of experience between us, in fact – and we’ve made it our mission to share that combined knowledge and expertise with you.
We’re here to provide an independent voice that cuts through all the noise to inspire, inform and entertain you; ensuring you get maximum enjoyment from your tech at all times. Technology is our passion, so let us be your expert guide.
years' experience
how-tos written
Apple events covered
Deals
All Deals-
-
 TechRadar Deals
TechRadar DealsBest Apple Memorial Day sales 2024: date and deals to expect
Your guide to this year's Memorial Day Apple sales event, with key information such as the date and deals to expect.
-

Don't miss the Samsung Galaxy S23 Ultra for just $849 at Best Buy right now
Best Buy has cut more than $500 off the Samsung Galaxy S23 Ultra, bringing the price down to just $849.
-

The best laptop deals in April 2024
Our expert guide to all the best laptop deals currently available.
-

AMD Radeon RX 7800 XT, one of the best midrange GPUs, is at its lowest price ever
One of the best midrange graphics cards on the market, the AMD Radeon RX 7800 XT, has reached an all-new low price.
-

Best Buy is slashing prices on our best-rated OLED TVs - save over $1,000 while you can
Best Buy is having a huge sale on our best-rated OLED TVs, and I'm rounding up the best deals with over $1,000 from Samsung and LG.
-

Huge Samsung Galaxy S24 sale: get our best-rated Android phone for a record-low price
Best Buy is running a sale on the Samsung Galaxy S24 range with savings of up to $200 available on all handsets.
-
-
-

OnePlus Coupons for April 2024
Use these OnePlus coupons to get a better price on mobiles & accessories from the leading Android smartphone retailer.
-

Microsoft Promo Code for April 2024
Use these Microsoft promo codes to save up to $500 off select Surface Pro 9 devices
-

Casper Coupons for April 2024
These Casper coupons can help you save big on your next bedding purchase from sheets, pillows, mattresses, and more.
-

Paramount Plus Coupon Codes for April 2024
Our Paramount Plus coupon codes can be added to your subscription to help you save on monthly streaming fees.
-
TechRadar's story

Our mission is unchanged
TechRadar was launched in January 2008 with the goal of helping regular people navigate the world of technology. It quickly grew to become the UK's biggest consumer technology site.
Expansions into the US and Australia followed in 2012 and we are now one of the biggest tech sites in the world.
- We've been covering tech since 2008
- 17 international editions from Mexico to New Zealand
- We're a globally respected brand worldwide
Software
All Software-
-

Meta’s massive OS announcement is more exciting than a Meta Quest 4 reveal, and VR will never be the same again
The surprise Meta Horizon OS announcement sets it up as VR’s Windows – and that’s both a great and terrible thing.
-

Microsoft could add yet another advert into Windows 11 - and users are running out of patience
Microsoft tests user patience with ads in Windows 11, sparking debate over integration, privacy, and the future of the Windows user experience.
-

Ray Ban’s Meta Glasses now let you listen to Apple Music with voice controls for maximum nerd points
The Ray-Ban Meta smart glasses now offer native Apple Music controls, and new WhatsApp and Messenger video call tools.
-

Meta Quest's software is coming to new Asus ROG and Lenovo headsets
Meta is opening the newly dubbed Horizon OS to third parties so they create more Quest headsets and port their apps over.
-
-
-

The best PlayStation VR deals in April 2024 - the latest prices on PSVR 2 and PSVR 1 sets
If you're looking for the best opportunity to get ahold of Sony's VR tech, we've compiled the best deals available.
-

Fortnite Festival's next major headlining star is Billie Eilish
Epic Games has announced that Fortnite Festival season 3 will feature pop star Billie Eilish.
-

PlayStation Portal restock tracker - the latest tips on where to check for stock
We're still tracking the PlayStation Portal restock situation for you, trying to give you the best advice on where to buy the PlayStation Portal remote play device.
-
 Review
ReviewPDP Riffmaster review - rock’s back on the menu
The PDP Riffmaster isn’t perfect, but is worth considering as a modern, readily available guitar controller.
-
Meet Your Experts
Between them, the TechRadar team have 300 years' experience in tech journalism. Here's why you should trust them.
-
-

Australian broadband provider nbn delivered 100 gigabit speeds using Nokia’s Lightspan MF fiber platform
Australian broadband provider nbn delivered 100 gigabit speeds using Nokia’s Lightspan MF fiber platform.
-

UnitedHealth confirms major cyberattack, says hackers stole "substantial" amount of patient data
UnitedHealth moves to assure victims with free credit and identity monitoring.
-

The future of software development: Low-code vs no-code
Dawid Przespolewski, Head of Business Development at Future Processing explores the future of no-code and low-code for business.
-

China somehow got its hands on advanced Nvidia chips, despite the sanctions
Nvidia chips are still being bought and sold in China, despite US sanctions banning the sale
-






























