Explore TechRadar
Reviews
All reviews-
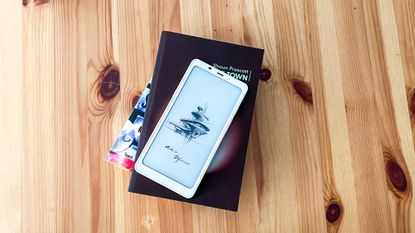
Onyx Boox Palma review: a tiny ereader like no other
The Onyx Boox Palma mimics a phone and is the most portable ereader I’ve had the pleasure of using.
-
-

Nike Ultrafly review: The carbon-plated off-road cruiser
It’s not a Vaporfly for the trails, but the Nike Ultrafly is still a comfy off-road cruiser.
-

Nothing Ear (a) review: mellow yellow earbuds to herald Nothing's purple patch
Has Nothing really done something impressive in the true wireless earbuds arena? Yes, with the inexpensive Ear (a).
-

Xiaomi 13T Pro review: a unique taste of flagship values
The Xiaomi 13T Pro stands as a proud middleman in Xiaomi's smartphone range and proves just how unique a phone can be whilst retaining the flagship experience we all crave.
-

Netgear Orbi 970 review: a state-of-the-art Wi-Fi 7 mesh system for larger homes and offices
Netgear's latest Orbi mesh router system offers best-in-class range and connection quality, but it's not exactly wallet-friendly.
-

Linksys Velop Pro 6E review: high-speed Wi-Fi for homes and offices of all sizes
While it might be too much for some users' at-home Wi-Fi needs, the Linksys Velop Pro 6E is a stellar choice of router.
-

Enabot Ebo SE pet robot review: the catsitter I didn’t know I needed but can’t live without
The Enabot Ebo SE is a cute companion bot that will keep you in touch with your special furry friend, and take loads of photos for you too!
-
How TechRadar tests

Product testing for the real world
You need to know that the device or service you’re about to spend money on works as advertised - and that it works in the real world.
- We test properly: objective and subjective testing
- We use experienced experts for our reviews
- We always offer 100 per cent unbiased, independent opinions
reviews
hours' testing
buying guides
Phones
All Phones-

Galaxy users claim they're running into infamous green line problem after update
Online reports state the green line affects both high-end and mid-range models, but no one can figure out why.
-
-

Google Pixel 8a renders tease new colors but an older design
New renders of the Google Pixel 8a clearly show four new colors and a familiar gentle curved design.
-

Five things the Xiaomi 14 Ultra's Photography Kit needs to truly elevate smartphone photography
The Xiaomi 14 Ultra's Photography Kit adds physical controls and photography-specific features to an already-capable camera phone – but it could do even more.
-

Grab the Google Pixel 7a for just $349 at Amazon right now
Get the Google Pixel 7a for just $349 in this great Amazon deal.
-

iOS 17 update lets you use AirPlay to stream movies in select hotels for the first time
Apple has updated iOS 17 so that AirPlay works in select hotels, letting you stream movies over the air.
-

OnePlus is launching two familiar but new devices – the OnePlus Pad Go and the OnePlus Watch 2 Lifestyle Edition
Both the OnePlus Pad Go and a new version of the OnePlus Watch are coming to Europe.
-

This Harry Potter Xiaomi Redmi Turbo 3 actually looks worthy of wizarding world
Redmi has launched a special Harry Potter Edition of its latest Turbo 3 phone.
-
Laptops & Computing
All Laptops & Computing-

Quordle today – hints and answers for Friday, April 19 (game #816)
Looking for Quordle clues? We can help. Plus get the answers to Quordle today and past solutions.
-
-

NYT Strands today — hints, answers and spangram for Friday, April 19 (game #47)
Looking for NYT Strands answers and hints? Here's all you need to know to solve today's game, including the Spangram.
-

NYT Wordle today — answer and hints for game #1,035, Friday, April 19
Looking for Wordle hints? We can help. Plus get the answers to Wordle today and yesterday.
-

DJI launches its own power stations to charge your drones when far from home
DJI's Power 500 and Power 1000 can both fast charge drones in about 30 minutes so long as you have the correct model.
-

Dear tech industry, we don't need to follow behind gaming with terrible product trade-in values
Trading in used components, like CPUs and GPUs, is difficult enough without retailers making it worse.
-

Fans are recreating tech history by building their own vintage 3dfx Voodoo graphics card
Fans are building their own 3dfx Voodoo, a custom vintage graphics card, from scratch.
-

These ChatGPT-powered glasses might be the future – but right now I’m disappointed
The Lucyd Lyte smart glasses might have ChatGPT integration, but overall they left me disappointed.
-
Apple
All Apple-

iOS 17 update lets you use AirPlay to stream movies in select hotels for the first time
Apple has updated iOS 17 so that AirPlay works in select hotels, letting you stream movies over the air.
-
-
 Updated
UpdatediPhone 16: release date speculation, latest leaks, price predictions and more
Here's everything we've heard so far about Apple's rumored iPhone 16 device, from its release date to its features.
-

The iPhone 16 Plus could be the last Plus model of its kind – here’s why
Apple will reportedly abandon the 6.7-inch iPhone display size with the iPhone 17 line.
-

The first third-party iOS app store is live in the EU – and another Nintendo emulator just showed up
The walled garden Apple has built around its iOS App Store continues to be slowly dismantled.
-

Apple says its recycling robots can now handle 23 different iPhone models – here’s how to recycle yours for free
Apple says it will recycle 23 different types of iPhone for free, so should you clear out your old devices?
-
Streaming
All Streaming-

Prime Video movie of the day: Mafia Mamma is the best kind of bad movie, in that it’s actually great
Does a movie need to make sense? Not if it's tons of fun.
-
-

Netflix movie of the day: The Matrix has you… knock knock
Wondering what to watch today? If in doubt, watch The Matrix…
-

Netflix sets Sweet Tooth season 3 return date for the post-apocalyptic series’ final chapter
The comic book adaptation will come to an "epic conclusion" in the third and final season of Sweet Tooth.
-
Apple TV Plus expands its epic sci-fi series lineup with For All Mankind season 5 and new Star City spinoff
It's blast-off for season five of For All Mankind, alongside a brand new spinoff show called Star City.
-
 Updated
UpdatedHow to watch the Batman movies in order: chronological and release date
Your guide to enjoying the Batman movies in order, from The Dark Knight to The Lego Batman Movie – and beyond...
-
TVs
All TVs-
-

Best Buy launches big-screen 4K TV sale - save up to $800 on Sony, LG and Samsung
A huge 4K TV sale is now live at Best Buy with savings of up to $800 available on a number of the best big-screen displays.
-

The Samsung QN90C is one of the best QLED TVs you can buy, and it's $1,300 off
The Samsung QN90C is rated as one of our best QLED TVs and the 75-inch model is on sale for a record-low $1,999.99.
-

Your Sky TV just got 10 times better with a load of useful free updates
Sky TV customers are getting a load of great free updates that make it easier to stream the movies and shows you love.
-

Sony's 2024 Dolby Atmos soundbar range has arrived - here's what you need to know
Two new soundbars, a wireless speaker system and a personal home theater neckband make up Sony's 2024 audio range.
-

Sony reveals 2024 TV range with next-gen mini-LED – here’s everything you need to know
Sony's 2024 TV range has arrived and the company has opted for mini-LED over OLED for its flagship model.
-

Samsung's stunning Frame TV is my dream display and it's now cheaper than ever
I've just spotted Samsung's stunning 75-inch The Frame QLED TV on sale for a new record-low price of $1,895 at Amazon.
-

Sharp’s new cheap Dolby Atmos soundbar undercuts Denon and Sonos but you'll need to wait for it
The new Sharp HT-SB700 soundbar looks like great value for money, but it's not made it outside of Europe just yet.
-
Audio
All Audio-
-

I listened to Sony’s new Bravia Theater Quad system, and it's full-fat Dolby Atmos without wires
Sony's new 4.0.4-channel wireless speaker system is a lifestyle-friendly package that doesn't compromise on sonic immersion.
-
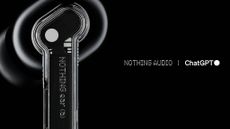
Nothing earbuds and phones are about to let you talk to ChatGPT for instant AI answers
Nothing beats rivals like Google to market, with plans to add ChatGPT to its phones and wireless earbuds, becoming the first to do this with a pinch-to-talk feature.
-

Nothing unveils 2 affordable earbuds with near-identical features – learn the key differences
Nothing Ear and Nothing Ear (a) are your confusingly named new wireless earbuds options.
-

Nothing Ear (a) review: mellow yellow earbuds to herald Nothing's purple patch
Has Nothing really done something impressive in the true wireless earbuds arena? Yes, with the inexpensive Ear (a).
-

Amazon Music is coming for Spotify’s AI playlists with new Maestro feature
Following the release of Spotify’s AI playlist generator, Amazon Music has joined the craze with its own AI feature Maestro.
-

Marshall drops two next-gen Bluetooth headphones with a major 100-hour battery life and minor price tags
Marshall updates its over-ears and buds to deliver better connections, improved sound quality and superb battery life
-

Motorola's new Moto Buds Plus offer Bose quality ANC and tuning for a budget price
Bose tuning, hi-rez audio, ANC and more – Motorola's new Moto Buds and Moto Buds Plus offer a lot for such a budget price.
-
Health & Fitness
All Health & Fitness-
-
 Buying guide
Buying guideThe best running shoes 2024: Hit the road with our top sneakers and trainers
We've tested the best running shoes for hard surfaces, with all distances and types of runners catered for
-

How to track a London Marathon 2024 runner: The official app, Garmin, Strava and more
How to track runners during this year’s London marathon.
-

Nike Ultrafly review: The carbon-plated off-road cruiser
It’s not a Vaporfly for the trails, but the Nike Ultrafly is still a comfy off-road cruiser.
-
Cameras
All Cameras-
-
 Updated
UpdatedThe best instant camera 2024
Our best instant cameras guide will help you find the best retro sidekick for you, whether your prefer Polaroid or Instax.
-
 Updated
UpdatedBest beginner DSLR cameras for 2024
Our round-up of the best beginner DSLR cameras will help you find the perfect entry-level option for your budget.
-

Blackmagic's new Pyxis 6K is an ultra-versatile Sony and Panasonic rival for indie filmmakers
Blackmagic's 6K modular 'box' camera is announced alongside the new Ursa Cine 12K, an Arri Alexa 65 rival 17K pro camera concept, plus the latest version of Davinci Resolve.
-
 News
NewsSony’s new 16-25mm is its lightest and smallest ever ultra-wide f/2.8 zoom lens, but it comes with a catch
Sony’s new ultra-wide zoom swaps focal range for compactness and makes a matching pair with the FE 24-50mm F2.8 G.
-
Home
All Home-
-

There's a huge Prime Day-like sale at Amazon - shop the 13 best deals from $20
Amazon's having a huge Prime-day-like sale on tech gadgets, and I've rounded up the best deals with prices starting at just $19.99.
-
 Updated
UpdatedThe best coffee maker 2024: top coffee machines for caffeine connoisseurs
Your tried-and-tested guide to the best coffee machines to help you unleash your inner barista.
-
 Updated
UpdatedThe best Nespresso machine 2024
The best Nespresso machines make incredible coffee of all kinds – and they do it with no mess and no fuss. Here are our top picks.
-

Enabot Ebo SE pet robot review: the catsitter I didn’t know I needed but can’t live without
The Enabot Ebo SE is a cute companion bot that will keep you in touch with your special furry friend, and take loads of photos for you too!
-
Buying guides
All Buying Guides-
 Buying guide
Buying guideThe best running shoes 2024: Hit the road with our top sneakers and trainers
We've tested the best running shoes for hard surfaces, with all distances and types of runners catered for
-
-
 Updated
UpdatedThe best instant camera 2024
Our best instant cameras guide will help you find the best retro sidekick for you, whether your prefer Polaroid or Instax.
-
 Buying guide
Buying guideBest crossplay games 2024: top titles for cross-platform play with friends
If you love multiplayer mayhem, you need the best crossplay games to enjoy with all your friends, no matter their platform of choice.
-
 Updated
UpdatedBest beginner DSLR cameras for 2024
Our round-up of the best beginner DSLR cameras will help you find the perfect entry-level option for your budget.
-
 Updated
UpdatedThe best coffee maker 2024: top coffee machines for caffeine connoisseurs
Your tried-and-tested guide to the best coffee machines to help you unleash your inner barista.
-
 Updated
UpdatedThe best Nespresso machine 2024
The best Nespresso machines make incredible coffee of all kinds – and they do it with no mess and no fuss. Here are our top picks.
-
 Buying Guide
Buying GuideBest Xbox Game Pass games to play in 2024
New to the service and wondering what the best Xbox Game Pass games are? Our curated list is here to help.
-
Why we're experts

We care passionately about tech
The TechRadar team has a life-long passion for the latest innovations – over 300 years of experience between us, in fact – and we’ve made it our mission to share that combined knowledge and expertise with you.
We’re here to provide an independent voice that cuts through all the noise to inspire, inform and entertain you; ensuring you get maximum enjoyment from your tech at all times. Technology is our passion, so let us be your expert guide.
years' experience
how-tos written
Apple events covered
Deals
All Deals-
-

Best Buy launches big-screen 4K TV sale - save up to $800 on Sony, LG and Samsung
A huge 4K TV sale is now live at Best Buy with savings of up to $800 available on a number of the best big-screen displays.
-

Grab the Google Pixel 7a for just $349 at Amazon right now
Get the Google Pixel 7a for just $349 in this great Amazon deal.
-
 TechRadar deals
TechRadar dealsVisible wireless plans guide: coverage, price, and everything you need to know
Looking for cheap unlimited data? Check out our guide to the best Visible wireless plans to find out everything you need to know.
-

GEEKOM A7 Mini PC is now $200 off
Don't miss this unique opportunity to get a great PC for a super low price.
-

The best cheap Amazon Fire tablet deals for April 2024
All the best Amazon Fire tablet deals that are available right now, including the HD, Kids and Kids Pro models.
-
 Deals
DealsMother's Day sales 2024: deals from Walmart, Lowe's, Amazon and more
Your 2024 Mother's Day sales guide with all the best deals from Walmart, Lowe's, and Amazon on gifts, jewelry, flowers, and more.
-
-
-

Microsoft Promo Code for April 2024
Use these Microsoft promo codes to save up to $500 off select Surface Pro 9 devices
-

OnePlus Coupons for April 2024
Use these OnePlus coupons to get a better price on mobiles & accessories from the leading Android smartphone retailer.
-

Casper Coupons for April 2024
These Casper coupons can help you save big on your next bedding purchase from sheets, pillows, mattresses, and more.
-

Paramount Plus Coupon Codes for April 2024
Our Paramount Plus coupon codes can be added to your subscription to help you save on monthly streaming fees.
-
TechRadar's story

Our mission is unchanged
TechRadar was launched in January 2008 with the goal of helping regular people navigate the world of technology. It quickly grew to become the UK's biggest consumer technology site.
Expansions into the US and Australia followed in 2012 and we are now one of the biggest tech sites in the world.
- We've been covering tech since 2008
- 17 international editions from Mexico to New Zealand
- We're a globally respected brand worldwide
Software
All Software-
-

These ChatGPT-powered glasses might be the future – but right now I’m disappointed
The Lucyd Lyte smart glasses might have ChatGPT integration, but overall they left me disappointed.
-

Windows 11’s Photos app is getting more sophistication with new Designer app integration - but there’s a catch
Windows 11's Photos app introduces Designer web app integration, offering advanced editing tools, but some encounter glitches and question Microsoft's editing tool strategy.
-

Clues in Windows 11 suggest Microsoft’s big AI feature for 24H2 update will be for Snapdragon X Elite laptops only
Is Microsoft going to push harder with ARM-based Windows 11 laptops by exclusively giving them its kingpin AI feature?
-

Pixel's new satellite feature could show people where you are on Google Maps
Recent leaks claim the Pixel 9 will see the launch of a location sharing on Maps and help guide for satellite connectivity.
-
-
-

Medieval RPG sequel Kingdom Come: Deliverance 2 is set to launch later this year
Kingdom Come: Deliverance 2 is set to launch later this year.
-

PlayStation Portal restock tracker - the latest tips on where to check for stock
We're still tracking the PlayStation Portal restock situation for you, trying to give you the best advice on where to buy the PlayStation Portal remote play device.
-

Larian Studios is working on adding crossplay and a photo mode to Baldur's Gate 3
Larian Studios has revealed its plans for Baldur's Gate 3, including what's to come in patch 7 and beyond.
-

The best video game remakes 2024
If you're looking for the best video game remakes - you can't go wrong with these essential and up-to-date picks.
-
Meet Your Experts
Between them, the TechRadar team have 300 years' experience in tech journalism. Here's why you should trust them.
-
-

Microsoft says Copilot app in Windows Server was a mistake
An update for Microsoft Edge triggered an error, pushing Copilot app into Windows Server.
-

TP-Link routers are still being bombarded with botnet and malware threats
A year later, multiple groups are still trying to abuse TP-Link flaw and install malware.
-

Seagate got a hard drive to work continuously over 6000 hours, transferring 3.2PB of data to prove its reliability
Seagate got a hard drive to work continuously over 6000 hours, transferring 3.2PB of data to prove its reliability.
-

A whole new generation of ransomware makers are attempting to shake up the market
Are hackers fed up with the Ransomware-as-a-Service model? Sophos thinks so.
-






























