Explore TechRadar
Reviews
All reviews-

Netgear Orbi 970 review: a state-of-the-art Wi-Fi 7 mesh system for larger homes and offices
Netgear's latest Orbi mesh router system offers best-in-class range and connection quality, but it's not exactly wallet-friendly.
-
-

Linksys Velop Pro 6E review: high-speed Wi-Fi for homes and offices of all sizes
While it might be too much for some users' at-home Wi-Fi needs, the Linksys Velop Pro 6E is a stellar choice of router.
-

Enabot Ebo SE pet robot review: the catsitter I didn’t know I needed but can’t live without
The Enabot Ebo SE is a cute companion bot that will keep you in touch with your special furry friend, and take loads of photos for you too!
-

NOMVDIC P2000UST-RGB
Stylish UST that impresses with its audio and daytime performance
-

Instant Pot Pro Plus Smart Multi-Cooker review
This 10-in-1 design lets you pressure cook, steam, sauté, slow cook and more, with control via a dedicated smart app.
-

CMF By Nothing Buds review: stylish budget earbuds with a vibrant flair
The CMF By Nothing Buds lack great ANC and reliable software, but they look cool and they’re incredibly cheap.
-

Nons SL660 review: an instant camera photographers will fall in love with
Manual control, striking looks, high build quality, swappable lenses – the Nons SL660 is a photographer's instant camera.
-
How TechRadar tests

Product testing for the real world
You need to know that the device or service you’re about to spend money on works as advertised - and that it works in the real world.
- We test properly: objective and subjective testing
- We use experienced experts for our reviews
- We always offer 100 per cent unbiased, independent opinions
reviews
hours' testing
buying guides
Phones
All Phones-

Instant Slow-mo is the coolest Galaxy AI feature you’re not using properly
Instant Slow-mo is now available on a range of Galaxy devices – here's how best to use the new AI-powered feature.
-
-

Samsung Galaxy AI compatibility explained: which phones are getting which features?
We round up the Samsung Galaxy devices which are (or soon will be) compatible with Galaxy AI.
-
Want a retro gaming emulator on your iPhone? Apple just clarified the state of play on iOS
Apple has clarified which gaming emulators are allowed on the iOS App Store, but will Nintendo be happy?
-

The new Moto Edge 50 series takes on Google Pixel phones with real design flair and solid specs
The Moto Edge 50 Pro and Edge 50 Ultra look set to lock horns with the Google Pixel 8 series.
-

Google's next foldable could be the Pixel 9 Pro Fold and finally get flagship specs
A new leak suggest all four models of the Pixel 9 series will share a similar chipset which could be the Tensor G4.
-

Samsung Galaxy Z Fold 6 colors: every rumored shade
The Samsung Galaxy Z Fold 6 is likely to land in five colors, and we've heard about some possible candidates.
-
 Updated
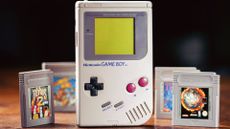
UpdatedThe first gaming emulators are now on the iOS App Store – and one has already been pulled
You can now use your iPhone as if it was a Commodore 64 or a Game Boy, thanks to newly added apps.
-
Laptops & Computing
All Laptops & Computing-

Google adds biometric verification to Play Store to keep your in-store wallet safe
Google Play Store's new security tool will ask you to verifiy your identify with either a fingerprint or face scan on Android.
-
-

Quordle today – hints and answers for Wednesday, April 17 (game #814)
Looking for Quordle clues? We can help. Plus get the answers to Quordle today and past solutions.
-

NYT Strands today — hints, answers and spangram for Wednesday, April 17 (game #45)
Looking for NYT Strands answers and hints? Here's all you need to know to solve today's game, including the Spangram.
-

NYT Wordle today — answer and hints for game #1,033, Wednesday, April 17
Looking for Wordle hints? We can help. Plus get the answers to Wordle today and yesterday.
-

A big WhatsApp update will soon make it easier to find your chats – here's how
WhatsApp adds four new filter buttons to the top of the home page so you can easily find unread messages and group chats.
-

Looking for a high-performance graphics card? Shop today's best deals from $689.99
The AMD Radeon RX 7900 XT and Nvidia GeForce RTX 4070 Ti Super graphics cards are both discounted right now.
-
 Tips from the experts
Tips from the experts5 tips from a hacker to keep you safe online
Get security advice from a real pen-tester, and see what steps I take to protect myself from other hackers. Boost your online safety with these 5 tips.
-
Apple
All Apple-

The latest macOS Ventura update has left owners of old Macs stranded in a sea of problems, raising a chorus of complaints
Users of macOS Ventura face firmware issues, lag, and bugs post-update, clamoring for fixes and for Apple's response.
-
-
Want a retro gaming emulator on your iPhone? Apple just clarified the state of play on iOS
Apple has clarified which gaming emulators are allowed on the iOS App Store, but will Nintendo be happy?
-
 Updated
UpdatedThe first gaming emulators are now on the iOS App Store – and one has already been pulled
You can now use your iPhone as if it was a Commodore 64 or a Game Boy, thanks to newly added apps.
-

Apple's M4 plans could make the latest MacBooks outdated already
Don't buy a new MacBook if this new M4 rumor is true - Apple may be planning new releases later this year.
-

Apple’s AI features in iOS 18 might only work on your device – here’s what that means
Apple’s AI tools in iOS 18 won’t rely on the cloud, which has implications for users' privacy, but also for their effectiveness.
-
Streaming
All Streaming-

Prime Video movie of the day: Blockers is a dumb raunchy comedy with a smart theme
A silly comedy about how modern parents maybe need to chill out.
-
-

Netflix movie of the day: LA Confidential is still a perfect period police thriller
The ultimate cable classic hits just as hard on streaming
-

Prime Video’s new Outer Range trailer suggests season 2 of the genre-bending sci-fi show will be even stranger
From a hole in the ground to astonishing revelations, Outer Range season two promises more Wyoming weirdness.
-

Disney Plus' possible cable-style Star Wars channel plan proves we're never getting rid of cable
A new rumor claims Disney Plus plans to add a few genre-based, cable-like programming channels.
-

Netflix has a surprise new smash show, Baby Reindeer – here are 3 more captivating thrillers to watch next
Baby Reindeer came out of nowhere, with a 100% score on Rotten Tomatoes – and there are more interesting thrillers on Netflix
-
TVs
All TVs-
-

Samsung's stunning Frame TV is my dream display and it's now cheaper than ever
I've just spotted Samsung's stunning 75-inch The Frame QLED TV on sale for a new record-low price of $1,895 at Amazon.
-

Sharp’s new cheap Dolby Atmos soundbar undercuts Denon and Sonos but you'll need to wait for it
The new Sharp HT-SB700 soundbar looks like great value for money, but it's not made it outside of Europe just yet.
-
 Hot deals
Hot dealsThe cheapest OLED TV deals and sales for April 2024
Your guide to the best OLED TV deals with incredible sales from brands like Sony, LG, and more.
-

Samsung’s new cheap 98-inch 4K TV with 120Hz support could be your dream gaming TV
Samsung is going all in on ultra-large screens for 2024, and its new 98-inch DU9000 packs powerful features for the price.
-

NOMVDIC P2000UST-RGB
Stylish UST that impresses with its audio and daytime performance
-

New OLED TVs are brighter than ever – here’s what that means for LCD's future
Samsung, Sony, TCL and more are launching ultra bright LCD TVs in 2024 but next-gen OLED is increasingly catching up.
-

I tried Klipsch’s affordable Dolby Atmos soundbar – and Sonos and Bose have been put on notice
Klipsch's new Flexus Core 200 is an impressive Dolby Atmos model that should shake up the budget soundbar space.
-
Audio
All Audio-
-

Marshall drops two next-gen Bluetooth headphones with a major 100-hour battery life and minor price tags
Marshall updates its over-ears and buds to deliver better connections, improved sound quality and superb battery life
-

Motorola's new Moto Buds Plus offer Bose quality ANC and tuning for a budget price
Bose tuning, hi-rez audio, ANC and more – Motorola's new Moto Buds and Moto Buds Plus offer a lot for such a budget price.
-

SoundMagic's new cheap USB-C earbuds have an onboard DAC for hi-res audio from iPhone or Android
The SoundMagic E11C had a 3.5mm termination, the E11BT went wireless, and now there's a USB-C option with an onboard DAC.
-

iFi's third-gen 'affordable' Zen DAC is in – and it's got a phono stage pal too
Take note, the new Zen DAC 3 comes with a $70 price hike over the original.
-

CMF By Nothing Buds review: stylish budget earbuds with a vibrant flair
The CMF By Nothing Buds lack great ANC and reliable software, but they look cool and they’re incredibly cheap.
-

Jabra Elite 10 review: Dolby Atmos sound in first class comfort
Jabra’s Elite 10 is a premium alternative to its sporty lineup of true wireless earbuds, with spatial audio, advanced ANC, long-lasting battery life and more.
-

I tried the Loop Switch 3-in-1 noise reduction earbuds to keep my sensory overload in check
Whether you struggle with sound sensitivity, want to protect your hearing, or just want some peace and quiet in the office, the Loop Switch 3-in-1 earbuds offer fantastic noise control.
-
Health & Fitness
All Health & Fitness-
-

How to run your first marathon in 2024: Expert advice for beginner runners
Running your first marathon? We asked the experts for their top tips.
-

A big Garmin Forerunner update is on the way – here are 5 new features we're excited about
Garmin has announced a new update for a number of models in its Forerunner line – these are the five key features to expect.
-

Oura Ring 4: latest news, rumors, and what we want to see
The 3rd-gen Oura smart ring was launched back in 2021, which means we're due a refresh.
-
Cameras
All Cameras-
-
 News
NewsSony’s new 16-25mm is its lightest and smallest ever ultra-wide f/2.8 zoom lens, but it comes with a catch
Sony’s new ultra-wide zoom swaps focal range for compactness and makes a matching pair with the FE 24-50mm F2.8 G.
-

I tested the Google Pixel’s Long Exposure photo mode – and it’s another reason to leave my pro mirrorless camera at home
Long exposure is a popular technique for landscape photography and Google Pixel's dedicated mode is surprisingly effective.
-

Nons SL660 review: an instant camera photographers will fall in love with
Manual control, striking looks, high build quality, swappable lenses – the Nons SL660 is a photographer's instant camera.
-

Insta360 could launch an 8K successor to the world's best 360 camera soon
Insta360 has announced a launch date for its next camera – and new leaks suggest it's for the Insta360 One X4.
-
Home
All Home-
-
 Updated
UpdatedThe best coffee maker 2024: top coffee machines for caffeine connoisseurs
Your tried-and-tested guide to the best coffee machines to help you unleash your inner barista.
-
 Updated
UpdatedThe best Nespresso machine 2024
The best Nespresso machines make incredible coffee of all kinds – and they do it with no mess and no fuss. Here are our top picks.
-

Enabot Ebo SE pet robot review: the catsitter I didn’t know I needed but can’t live without
The Enabot Ebo SE is a cute companion bot that will keep you in touch with your special furry friend, and take loads of photos for you too!
-
 Updated
UpdatedThe best air fryer 2024
We've tested the best air fryers from all the biggest brands including Philips, Ninja, Instant Pot and more.
-
Buying guides
All Buying Guides-
 Updated
UpdatedThe best coffee maker 2024: top coffee machines for caffeine connoisseurs
Your tried-and-tested guide to the best coffee machines to help you unleash your inner barista.
-
-
 Updated
UpdatedThe best Nespresso machine 2024
The best Nespresso machines make incredible coffee of all kinds – and they do it with no mess and no fuss. Here are our top picks.
-
 Buying Guide
Buying GuideBest Xbox Game Pass games to play in 2024
New to the service and wondering what the best Xbox Game Pass games are? Our curated list is here to help.
-
 Updated
UpdatedThe best air fryer 2024
We've tested the best air fryers from all the biggest brands including Philips, Ninja, Instant Pot and more.
-
 Updated
UpdatedThe best home security camera 2024
We've tested the best security cameras from all the big brands. These are the best ones you can buy
-

The best laptop 2024: top portable picks for all budgets
Our best laptops guide can help you find the perfect device, no matter what your budget is.
-
 Updated
UpdatedThe best processor 2024
We've carefully selected the best CPU picks to get your PC running fast and efficiently.
-
Why we're experts

We care passionately about tech
The TechRadar team has a life-long passion for the latest innovations – over 300 years of experience between us, in fact – and we’ve made it our mission to share that combined knowledge and expertise with you.
We’re here to provide an independent voice that cuts through all the noise to inspire, inform and entertain you; ensuring you get maximum enjoyment from your tech at all times. Technology is our passion, so let us be your expert guide.
years' experience
how-tos written
Apple events covered
Deals
All Deals-
-
 Deals
DealsMother's Day sales 2024: deals from Walmart, Lowe's, Amazon and more
Your 2024 Mother's Day sales guide with all the best deals from Walmart, Lowe's, and Amazon on gifts, jewelry, flowers, and more.
-

Looking for a high-performance graphics card? Shop today's best deals from $689.99
The AMD Radeon RX 7900 XT and Nvidia GeForce RTX 4070 Ti Super graphics cards are both discounted right now.
-

Walmart Plus members just got a great free gaming perk
A new perk has been added for Walmart Plus members and you can now get Xbox Game Pass Ultimate for free for two months
-
 Hot deals
Hot dealsThe cheapest OLED TV deals and sales for April 2024
Your guide to the best OLED TV deals with incredible sales from brands like Sony, LG, and more.
-

Amazon just dropped one of this year's best tablet deals – and it's not the iPad
One of this year's best tablet deals is now available at Amazon and it's on a model we never expected to see again.
-

The best laptop deals in April 2024
Our expert guide to all the best laptop deals currently available.
-
-
-

Microsoft Promo Code for April 2024
Use these Microsoft promo codes to save up to $500 off select Surface Pro 9 devices
-

OnePlus Coupons for April 2024
Use these OnePlus coupons to get a better price on mobiles & accessories from the leading Android smartphone retailer.
-

Casper Coupons for April 2024
These Casper coupons can help you save big on your next bedding purchase from sheets, pillows, mattresses, and more.
-

Paramount Plus Coupon Codes for April 2024
Our Paramount Plus coupon codes can be added to your subscription to help you save on monthly streaming fees.
-
TechRadar's story

Our mission is unchanged
TechRadar was launched in January 2008 with the goal of helping regular people navigate the world of technology. It quickly grew to become the UK's biggest consumer technology site.
Expansions into the US and Australia followed in 2012 and we are now one of the biggest tech sites in the world.
- We've been covering tech since 2008
- 17 international editions from Mexico to New Zealand
- We're a globally respected brand worldwide
Software
All Software-
-

Google adds biometric verification to Play Store to keep your in-store wallet safe
Google Play Store's new security tool will ask you to verifiy your identify with either a fingerprint or face scan on Android.
-

A big WhatsApp update will soon make it easier to find your chats – here's how
WhatsApp adds four new filter buttons to the top of the home page so you can easily find unread messages and group chats.
-

The Microsoft Store gets a turbo boost in new update, promising speedier and sleeker performance
Microsoft Store's version 22403 brings significant performance upgrades, promising faster loading times and a smoother user experience, aiming for greater overall user satisfaction for the app.
-

The latest macOS Ventura update has left owners of old Macs stranded in a sea of problems, raising a chorus of complaints
Users of macOS Ventura face firmware issues, lag, and bugs post-update, clamoring for fixes and for Apple's response.
-
-
-

The AOKZOE A2 Ultra could be Intel's chance for a PC gaming handheld redemption
Intel may be getting a second shot at a PC gaming handheld with the AOKZOE A2 Ultra.
-

Reports rolling in that Steam Deck OLEDs seem to develop cracks on its cases
If you have a Steam Deck OLED, beware as several reports of cracks forming on its cases roll in.
-

Arrowhead says it will be making changes to Helldivers 2's 'ridiculous' fire damage
Arrowhead Game Studios has confirmed that it will be making changes to Helldivers 2's flame system soon.
-

Best single-player games on Game Pass
We've pulled together all the best single-player games on Game Pass so you'll know which ones are worth playing.
-
Meet Your Experts
Between them, the TechRadar team have 300 years' experience in tech journalism. Here's why you should trust them.
-
-

Scientists at KAIST have come up with an ultra-low-power phase change memory device that could replace NAND and DRAM
Scientists at KAIST have come up with an ultra-low-power phase change memory device that could replace NAND and DRAM.
-

Crypto miner arrested for skipping on millions in cloud server bills
A Nebraska man ‘cryptojacked’ two cloud providers in a scheme with bleak economic and environmental implications.
-

A sneaky new steganography malware is exploiting Microsoft Word — hundreds of firms around the world hit by attack
TA558 is back, exploiting an age-old flaw in Microsoft Word to drop various infostealers.
-

Namecheap's Spaceship celebrates one year
Namecheap's one stop website service platform for website building and hosting celebrates its first birthday
-






























