Is retaliation the only way to stop cyberattacks?
Using trickery to outwit the cybercriminals

In war, sometimes the best defence is a good offence. By crippling an opponent's weapons, causing chaos and confusion, or disabling their infrastructure, it is possible to thwart an impending attack.
To fight cybercrime, governments may also need to conduct retaliatory measures. Of course, there is the pesky problem of international laws and even knowing which enemy to attack, but security experts say a certain level of counter-cyberterrorism might be warranted as the cyberwar escalates.
Benjamin Wrightis an attorney, instructor at the SANS Institute, and book author who told TechRadar.com about several ways cyber retaliation could work, and that in some cases it may be the only way to stop cybercriminals from infesting computers with botnets and malware.
Wrightsays the security field is full of nuance - there is no easy way to make one sweeping strike at an online adversary, suggesting that the UK or US would not be able to infect a spam purveyor overseas or take down a malware company with just one virus or counter-attack.
Instead, there are other forms of what he calls cyber-trickery that could be much more effective anyway, and more legal.
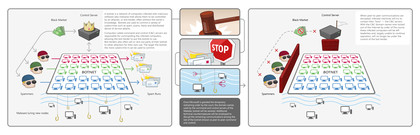
HOW BOTNETS WORK: This Microsoft description of how a worldwide botnet works shows the main command and control center is disabled. Image courtesy of Microsoft
Sign up for breaking news, reviews, opinion, top tech deals, and more.
One tactic currently in use is to predict how botnets can damage computer systems, and to write programs that automatically disable them. He says another approach that is used is to send fake data to a phishing scam site and overload it so that the data collection is useless.
Another approach, he says, is for government agencies to dissect the spam files, viruses, and malware to learn the identity of the cybercriminals. For example, there could be an IP address hidden in the code or as part of the spam message that governments could use to track down the perpetrators.
None of these measures are overly aggressive or hostile. Security expert Randall Pouliot, who worked as a penetration test team leader for the US government, says infecting the infectors is not wise.
"A government attacking another sovereign nation would violate international law and would also open the attacker to potential attribution unless they have deployed extremely sophisticated proxying techniques which would improve potential obfuscation," says Pouliot.
"If the cybercriminal were within US borders then US Code would apply. I'd expect computer or network attack would run the gambit from surreptitious data alteration to cause preferred effects to a straight out DDoS."
That said, one of the best counter-attacks involves legal action. Last year, Microsoft used this approach against the Waledac botnet, which had sent about 1.5 billion spam messages per day.
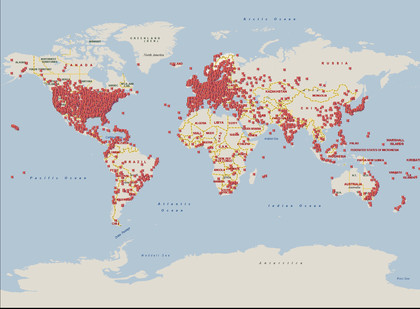
WALEDAC: Before taking civil action against the Waledac botnet, the spamming agent attacked these worldwide locations [Image credit: Microsoft]
Microsoft filed a civil action against Waledac and shut down the service. Since then, a few off-shoot botnots have sprung to life, many using the fast-flux method of quickly changing domain names, but the original host is now comatose and not capable of replicating, making any new related botnet attacks much less likely.
"A lawsuit is just one of many steps a defender can take to establish legal justification," says Wright."Another step is to post legal terms and conditions on the defender's network that say the attacker consents to the defender taking appropriate security measures to thwart him."
Pouliot says counter-assaults are probably an everyday occurrence, carried out by every government entity in the world, but there is no hard evidence that they are effective.
Still, the issue is being addressed. Last week, the FBI in the US announced they will research new counter-measures against terrorists and hacktavists who use social networks, private chat software like IRQ, and IP phone systems like Skype to communicate in real-time.
Wright says the FBI has to move to more sophisticated surveillance techniques because most of the reporting they do now is in capturing existing data but not in monitoring real-time or near-real-time communications on private nets.
--------------------------------------------------------------------------------------------------
Liked this? Then check out Who's hacking your PC?
Sign up for TechRadar's free Week in Tech newsletter
Get the hottest tech stories of the week, plus the most popular reviews delivered straight to your inbox. Sign up at http://www.techradar.com/register

John Brandon has covered gadgets and cars for the past 12 years having published over 12,000 articles and tested nearly 8,000 products. He's nothing if not prolific. Before starting his writing career, he led an Information Design practice at a large consumer electronics retailer in the US. His hobbies include deep sea exploration, complaining about the weather, and engineering a vast multiverse conspiracy.

 Become a TechRadar Insider
Become a TechRadar Insider







