Could your mystery program be malware that's found a way through your antivirus defences?
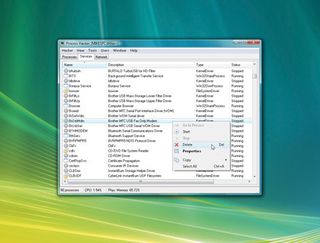
To find out, we start with some of the Process Hacker tests we've applied already. Either click the Network tab to see if the process is making a connection online, or right-click the process, select 'Properties | Handles' and check to see which files and Registry keys it's watching.
Next, try right-clicking the process, selecting 'Properties' and clicking the Memory tab. This will not only show you the various blocks of RAM owned by the process, but also let you search them. Choose 'String Scan' in the Search box and Process Hacker will browse through each memory block and report any ASCII strings that it finds.
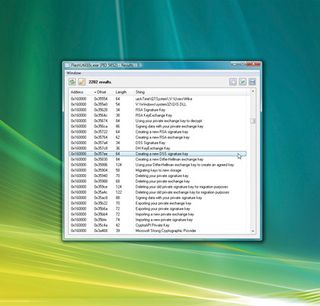
If a program has, say, been secretly collecting credit card numbers or reading important files, you may see the results show up here. You may also see interesting blocks of data that are part of the program's code: Registry keys it browses, filenames it's looking for, URLs it may try to reach or even prompts to be displayed later.
This catch-all nature makes memory searches handy for exploring legitimate programs, too. Unfortunately, Malware developers can use tricks to conceal information from memory scans. If all else fails, use your antivirus software to scan the file.
Right-click the mystery process, select 'Miscellaneous | Upload to VirusTotal' and the program will immediately send the file to www.virustotal.com, where it'll be scanned by around 40 antivirus tools. A browser window will open to let you know the result.
Some malware will attempt to avoid detection entirely by hiding its processes, but Process Hacker can be useful here, too. Click 'Tools | Hidden Processes' and then 'Scan', and the program will apply a simple but effective technique to find some hidden processes.
Get daily insight, inspiration and deals in your inbox
Get the hottest deals available in your inbox plus news, reviews, opinion, analysis and more from the TechRadar team.
If it doesn't find anything, choose the 'Brute Force' option and click 'Scan' again. This isn't particularly advanced technology and is no substitute for a specialist rootkit detection tool, but it's quick and worth a try if you suspect possible infection.
Take action
So far, we've focused on Process Hacker's monitoring tools, which tell you about the processes running on your PC. However, it also has some useful ways to interact with those processes that can help you manage your PC.
If a particular process is consuming an unusually large amount of RAM, for instance, right-click it and select 'Reduce Working Set', and Process Hacker will ask Windows to trim this down to something more manageable. This isn't a magic bullet, and if the process is actively using that RAM then the Working Set figure will start to grow again and quickly be back where it was, but it's worth a try.
Sometimes processes do much more than hog memory, grabbing all your CPU time and interfering with other applications. In this case, we'd try right-clicking the process, selecting 'Affinity' and ensuring only one box is checked. This restricts the process to one CPU core, leaving the others available for everything else.
You could also try right-clicking the process, selecting 'Priority' and reducing its priority a little – below Normal is best, but Idle will do if all else fails. The program will continue to run, but Windows will allocate it less CPU time overall, so it shouldn't interfere with other applications.
If a program is out of control or is unresponsive, then you may want to close it down. Right-click the process name and select 'Terminate Process' to close the process alone, or select 'Terminate Process Tree' to close it and any other processes it's launched.
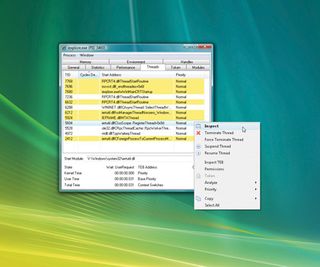
But be careful! Closing a system process could lock up your PC, and selecting 'Terminate Process Tree' for Explorer.exe will also close all the processes it's launched, including all your Windows start-up programs.
Occasionally, a program will lock up so completely that the regular Terminate option won't work. You'll probably have come across similar situations before, when even the Task Manager 'End Process' option won't kill a particular program. Luckily, Process Hacker has an extra function that just might do the job.
Right-click the process, select 'Terminator | Run' and Process Hacker will apply up to 16 ingenious methods to close it down and clean up afterwards. It's a powerful feature-set, and if Process Hacker works for you then there's an easy way to ensure it's always quickly available.
Click 'Hacker | Options | Advanced', check 'Replace Task Manager with Process Hacker' and click 'OK'.
Pressing [Ctrl]+[Shift] +[Esc] will now launch Process Hacker, making it easy to monitor everything running on your PC.
- 1
- 2
Current page: Finding malware that's beaten your AV
Prev Page Troubleshoot your PC with Process HackerMost Popular


